- Home
- Computing
Computing
About
News, reviews, and discussion about desktop PCs, laptops, and everything else in the world of computing, including in-depth buying guides and daily videos.

How to choose the best RAM for your PC in 2024






Gigabyte just confirmed AMD’s Ryzen 9000 CPUs
Even the new mid-tier Snapdragon X Plus beats Apple’s M3
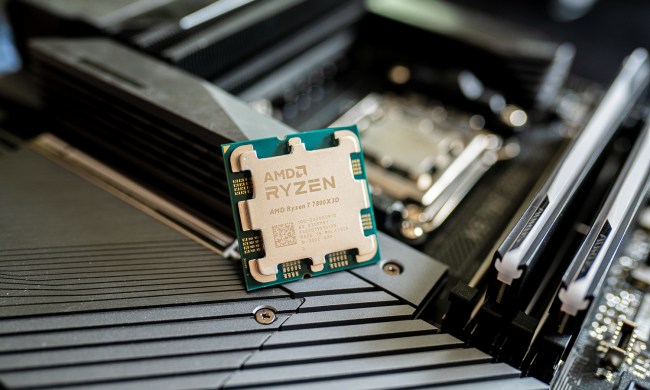
4 CPUs you should buy instead of the Ryzen 7 7800X3D

This Alienware gaming PC with an RTX 4090, 64GB of RAM is $1,000 off


The 10 best monitors for 2024: tested and reviewed

The Razer Blade RTX 40 series gaming laptops are on sale right now

Surface Pro 10: all the major changes rumored for the new model

Meta Smart Glasses just got the AI upgrade I’ve been waiting for

How to check your CPU temperature

Snag this 34-inch LG Curved Ultrawide WQHD monitor for $249

Save $300 on this HP desktop PC with an RTX 3060, 1TB SSD

Razer made the best gaming mouse even better

A Redditor ‘didn’t know’ about the Steam Deck, so they built their own

Windows 11 Home usually costs $139 — but it’s only $30 today

5 web browsers you should use instead of Google Chrome or Edge

How to double space in Microsoft Word
How to do a hanging indent in Microsoft Word
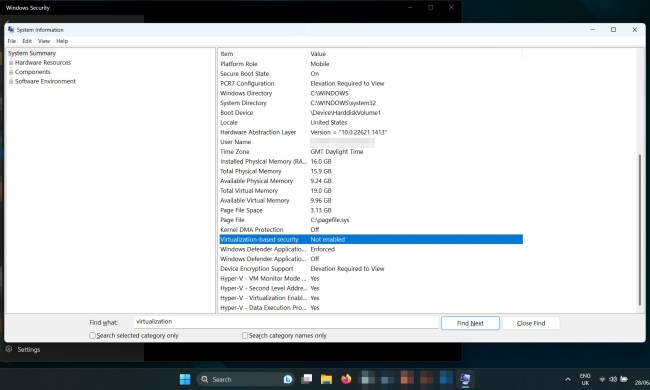
How to disable VBS in Windows 11 to improve gaming

How to do hanging indent on Google Docs

LG just knocked $300 off this 16-inch lightweight laptop

How to download a video from Facebook
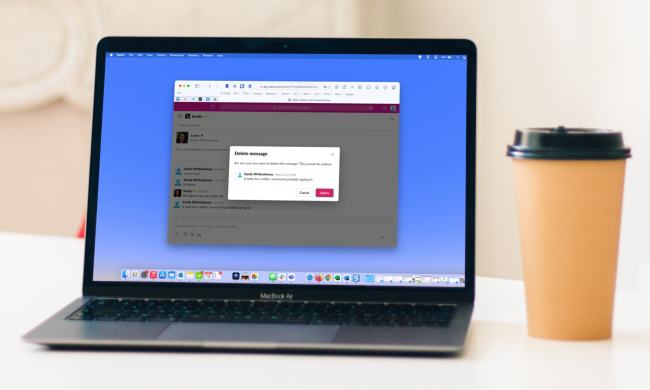
How to delete Slack messages on desktop and mobile
Computing News
Laptops
Computing Reviews
Nvidia
Luke Larsen is a Senior Editor at Digital Trends and manages all content covering laptops, monitors, PC hardware, and everything else that plugs into a computer. Luke joined Digital Trends in 2017 as a native Portlander, happy to join a media company that called his city home. His obsession with technology is in observing the ebb and flow of how technological advancement and product design intersects with our day-to-day experience of it. From digging into the minute details to stepping back and seeing the wider trends, Luke revels in telling stories with tech.
Before working at DT, he worked as Tech Editor at Paste Magazine for over four years and has bylines at publications such as IGN and The Oregonian. When he’s not obsessing over what the best laptop is or how Apple can fix the Mac, Luke spends his time playing designer board games, quoting obscure Star Wars lines, and hanging with his family.