Fortunately, the exploit has already been resolved, but by the time Valve fixed the bug at the heart of the problem, the damage had already been done. What makes this particular security issue different isn’t the severity of the problem, but the ease with which pretty much anyone could take over a Steam account once they knew of the exploit.
A YouTube user by the account name Elm Hoe illustrated the method in a video. It started by requesting a password reset on the targeted account. On the next screen the user is prompted to enter an authentication code in order to proceed with the reset. The exploit worked by simply not entering a code and skipping ahead.
At this point, the attacker was free to change the account password to one of their choosing, locking the actual owner of the account out in the process. Luckily, this exploit didn’t last for long: Valve learned of the exploit on July 25, and it seems that accounts had only been hijacked using this method starting July 21.
Once Valve learned of the bug it was quickly fixed, and any accounts that were suspect had their passwords reset. “Please note that while an account password was potentially modified during this period the password itself was not revealed,” the company said in a statement to Kotaku.
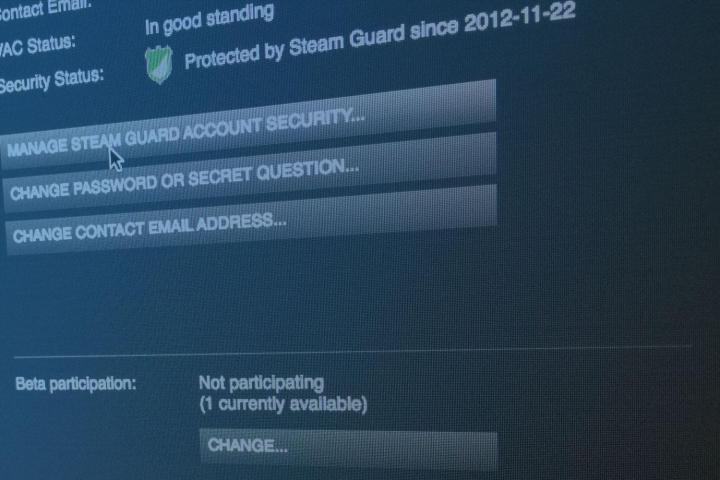
Valve was also quick to point out that any user accounts with Steam Guard enabled were protected from another person actually logging into their account, even if the account’s password was modified. It’s worth noting that this is yet another reason why you should have two-factor authentication enabled everywhere it is possible to do so.
For a look at how exactly the exploit was accomplished when it was still in the wild, see the video below.


