While it’s not malware-related, installing TrueCaller could have left you susceptible to malicious hackers. Cheetah Mobile’s Security Research Lab found a loophole in the app that would have allowed anyone to gain access to TrueCaller user’s private information. TrueCaller used a smartphone’s IMEI number as the identity label of its users.
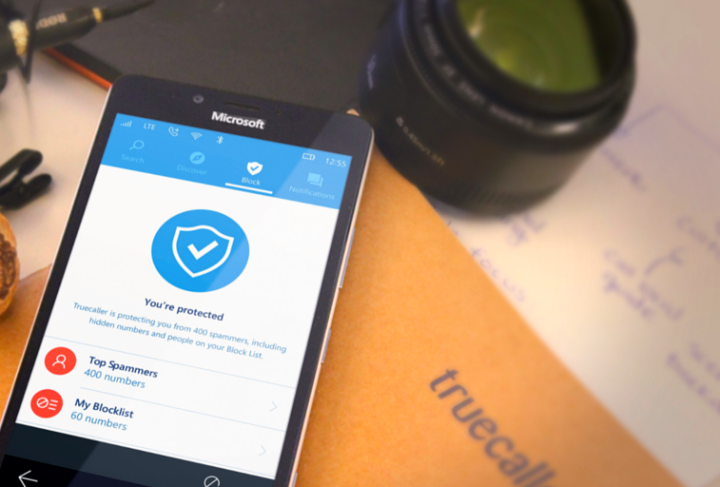
TrueCaller tells you who’s calling. It does so by identifying numbers, and matching them with ones marked by users. You can mark numbers as spam to make the service better and more reliable. As it crowd-sources its data, TrueCaller users have accounts with their name, phone number, home address, gender, and more — it’s this data that was available to malicious hackers through the app’s loophole.
If someone managed to get hold of your IMEI number, they could go to TrueCaller’s website and access all of that information in your account, and even modify it — potentially lifting spam blocks so those calls can make it through again.
Thankfully, TrueCaller has patched the issue, and you should download the latest update through the Google Play store to make sure you’re safe. The company says no user information was compromised.
“We recently found an issue where some user defined information can be retrieved or changed without the original user’s consent, if a third person knows the IMEI number of the original person’s device,” according to the blog post. “We’ve quickly taken steps to fix this issue and have released an update which we strongly suggest all users upgrade to.”
What makes it scary is that more than 100 million Android users who have downloaded the app were vulnerable, and likely more as TrueCaller has been making its way to Cyanogen OS, in phones like Wileyfox, and Blu devices. TrueCaller is also available for Windows, and iOS, but it looks like the app on those operating systems were not affected.
Editors' Recommendations
- Truecaller brings AI-powered spam call filtering to any iOS or Android phone
- Massive iPhone security flaw left millions of phones vulnerable to hacks
- Adobe left millions of Creative Cloud user records exposed online


