Researchers from Duke University, Penn State University and Intel Labs developed a piece of software called TaintDroid, which has been able to detect and report when applications transmit private information to remote servers.
Of the 30 applications tested with TaintDroid, 15 were found to be sending private information to advertising servers without informing users. That information included a phone’s SIM card number, GPS location and phone number.
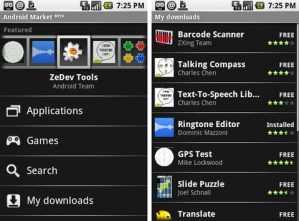
And these weren’t just any Android applications. Researchers used the thirty most popular applications across 22 categories which required Internet permission, along with permission to access location, camera, or audio data.
Users put their faith in application developers and the fact is that, “Android’s coarse grained access control provides insufficient protection against third-party applications seeking to collect sensitive data,” wrote the researchers involved in this study.
A Google representative has responded to the report, saying, “In all computing devices, desktop or mobile, users necessarily entrust at least some of their information to the developer of the application. Android has taken steps to inform users of this trust relationship and to limit the amount of trust a user must grant to any given application developer. We also provide developers with best practices about how to handle user data.”
This doesn’t leave users with many options. Sure, you can try to put faith in application developers, but the fact is that until stricter security standards are put in place, many Android applications may continue sharing your data.
Editors' Recommendations
- Every Android tablet we’re expecting in 2024
- How to find your lost phone (tips for iPhone and Android)
- Android 15 release date: When will my phone get the update?
- Google just released the first Android 15 beta. Here’s what’s new
- The 10 best photo editing apps for Android and iOS in 2024
