- Home
- Computing
Computing
About
News, reviews, and discussion about desktop PCs, laptops, and everything else in the world of computing, including in-depth buying guides and daily videos.

This excellent Lenovo laptop makes the Dell XPS 14 look overpriced






The best 5K monitors you can buy for max resolution

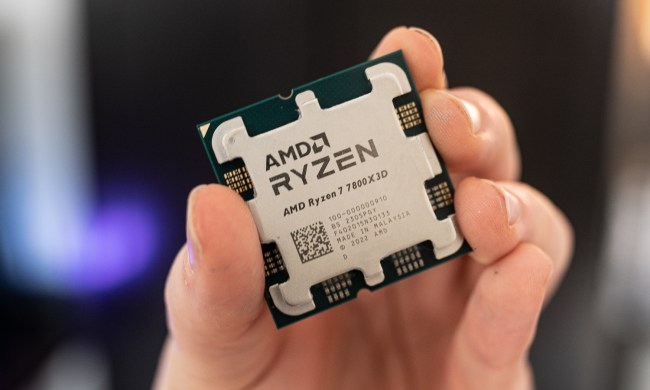
9 best processors for PC gaming: tested and reviewed

These 4K monitors are discounted at Best Buy — from $200

The XPS 16 is fighting an uphill battle against the MacBook Pro


These 6 tweaks take MacBooks from great to nearly perfect

My most anticipated laptop of the year just got leaked

These TP-Link mesh Wi-Fi systems are up to 40% off right now

The 5 best laptops for architects in 2024

Ghost of Tsushima is already shaping up to be a monster PC port

Lenovo sale: Get up to 67% off ThinkPad Laptops, from $600

Alienware sale: Get up to $1,000 off gaming laptops and PCs

How to set up Windows 11 without a Microsoft account

Best Buy’s deal of the day is $150 off the MacBook Air M2

The 6 best 2-in-1 laptops for drawing in 2024

Does RAM speed matter for PC performance?

Quest Pro 2: What we know about Meta’s next premium VR headset

The best processor for video editing in 2024 across all budgets

Don’t download the latest macOS Ventura update just yet

Best 14-inch laptops for 2024: tested and reviewed

RTX 4090 owners are in for some bad news

Razer, somehow, made a mouse pad exciting
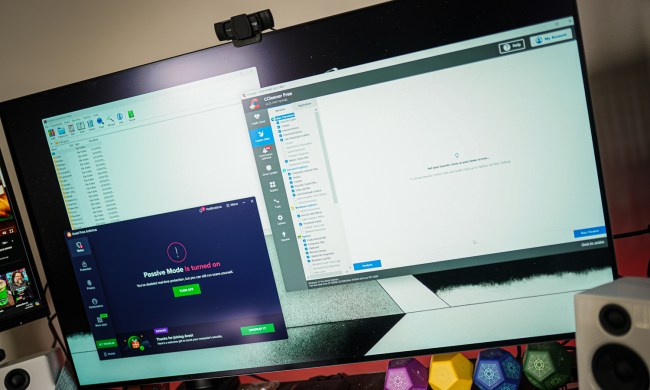
These are the PC apps you’re still using — but probably shouldn’t be
Computing News
Laptops
Computing Reviews
Nvidia
Luke Larsen is a Senior Editor at Digital Trends and manages all content covering laptops, monitors, PC hardware, and everything else that plugs into a computer. Luke joined Digital Trends in 2017 as a native Portlander, happy to join a media company that called his city home. His obsession with technology is in observing the ebb and flow of how technological advancement and product design intersects with our day-to-day experience of it. From digging into the minute details to stepping back and seeing the wider trends, Luke revels in telling stories with tech.
Before working at DT, he worked as Tech Editor at Paste Magazine for over four years and has bylines at publications such as IGN and The Oregonian. When he’s not obsessing over what the best laptop is or how Apple can fix the Mac, Luke spends his time playing designer board games, quoting obscure Star Wars lines, and hanging with his family.