There’s no denying that the Heartbleed bug is scary. In fact, it’s arguably the widest and deepest security hole ever discovered on the Web, reportedly leaving roughly two-thirds of the world’s websites at risk.
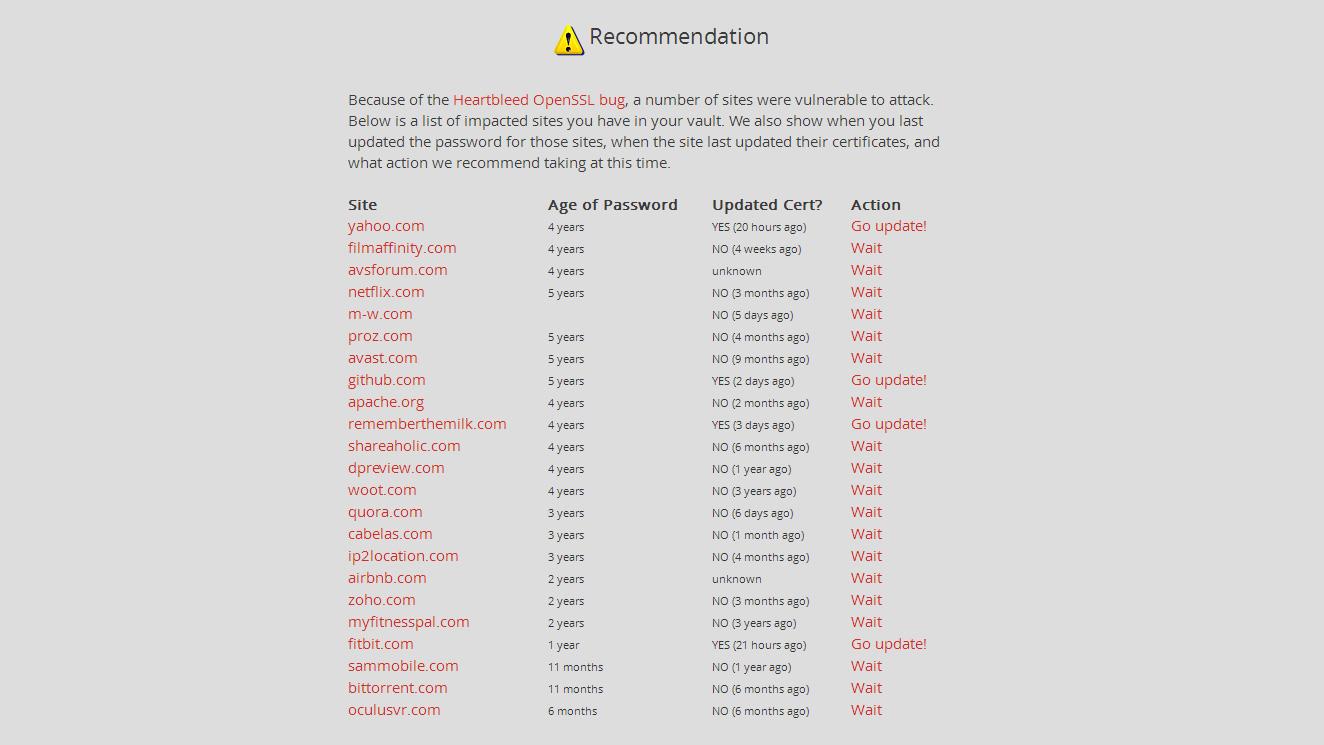
So if you haven’t done so yet, you should check every site that you have an account with to see if it is or was using the version of OpenSSL that is vulnerable to the bug. Also, check whether those vulnerable sites have fixed their Heartbleed wounds yet, by updating their security certificates.
With LastPass, you can make sure you’re using a different password for each site.
There’s no point in updating all your passwords yet, because many sites are still vulnerable to the bug, and all indications are that it will take at least several weeks before all the affected websites have patched the Heartbleed hole.
So what should you do in the meantime? A great first step would be to upgrade your Web security measures so that a hacker will need more than just your password to access your most important accounts (like, say, Google, PayPal, and Dropbox). You should also start using a password manager, like LastPass, so that when the next big security issue hits, you’ll know exactly which passwords you’ll need to change. With LastPass, you can make sure you’re using a different password for each site, and (if you opt for the $12-a-year premium account) you can use an app on your smartphone to autofill all your passwords, which makes changing them a whole lot easier.
But first, let’s talk about two-factor authentication.
Two-factor authentication is a great defense against leaked passwords
When news of Heartbleed first hit, I was surprised, but not that worried. Why? Because I set up two-factor authentication on many of my most important accounts ages ago.
Two-factor authentication is sometimes also called 2FA, or two-step verification. With this set up, when you log into an account on a device you haven’t used before, you have to provide both your password and something else—a second form of authentication.
Usually, that second form of verification comes in the form of a time-sensitive, one-time-use numerical code that gets sent to you in seconds via text message. So you’ll need to have your phone with you when logging into a computer or other device that you haven’t previously used that service with. It’s a minor inconvenience to have to enter an extra code, but chances are that you aren’t logging into Gmail or Facebook on unfamiliar devices all that often.
Besides, an occasional minor inconvenience is well worth the security of knowing that, even if someone somehow snags your Gmail or PayPal password, they can’t log in and start making purchases because they don’t also have access to your smartphone.

Each site that offers two-factor authentication has their own way of enabling it. But usually, it’s buried in the settings or account screens, and are not that hard to find. Of course, there are plenty of sites that don’t yet offer two-factor authentication (get on that, Amazon). However, you can see a definitive list of major sites that do and don’t offer it here, where you’ll also find links to instruction pages for sites that do offer the service. If an important site you use doesn’t yet offer two-factor authentication, there’s a good chance that they’re working on it now, especially after being forced to deal with the Heartbleed mess.
You may not want to set up two-factor authentication for every site that offers it. However, you should definitely do so for any site that has access to your finances (like banks), as well as Google (especially if you use Android or Gmail), and your social media accounts too. Cloud storage services, like Dropbox, should be on that list as well.
It’s time to use a password manager
Also, unless you specifically only use the Web for a few things, like email, Facebook, and casual Web browsing, you really should start using a password manager. There are quite a few out there, like RoboForm, Norton Identity Safe, and 1Password, but I’ve used LastPass for a couple years now, and have been quite happy with it. It’s also considered by many experts to be the best, because of its power and flexibility.
You should definitely set up two-factor authentication for any site that has access to your finances.
Your passwords should also consist of a combination of numbers, special characters, upper- and lower-case characters, and be at least eight characters long. Can you remember a different password like that for each of the sites you have accounts with? Probably not, and even if you could, you should also change your passwords on a regular basis (once every few months is a good general rule, especially for critical accounts).
Without a password manager, you’ll have a very hard time doing all that. But with LastPass, you can automatically generate strong passwords, see how old the passwords you’re using are, and automatically log into sites on your PC or Mac. That way, you don’t have to suffer the frustration of a forgotten password anymore—all for free.
Now, when using a password manager that stores all your passwords, even if the data is encrypted, like it is with LastPass, you are in some sense putting all your passwords behind one single password, which is potentially very dangerous. So you’ll want to make absolutely sure your LastPass password is unique, and very strong.
Beyond that, especially if you regularly use a smartphone or tablet, it’s probably worth it to spring for LastPass Premium. The service costs a fairly modest $12 per year, and gives you access to a couple of very important features.
With LastPass Premium, you can add two-factor authentication to your LastPass account (which, remember, will now house all your other passwords). Plus, with the Premium service, you’ll also have access to LastPass’ mobile apps for iOS, Android, Windows Phone, and BlackBerry, which will either automatically log you into sites on your mobile device, or let you copy and paste in your passwords. Just remember not to stay logged into the service all the time, in case your phone gets lost or stolen.
If you think $12 a year is expensive for that service, imagine manually keying in every unique, lengthy password for every site that gets an eventual Heartbleed patch. When that nightmare thought-bubble bursts, $12 probably won’t sound so bad.
Conclusion
As with all security-oriented articles, it’s important to point out that there are no guarantees that taking these steps (or any steps) will keep you safe while you traverse through the minefield that is the Internet, especially in this post-Heartbleed world. Even if you abandon the Web and your apps altogether, there’s enough data being collected and passed around about you, from your purchases, travel, etc., that some form of identity theft is always a possibility, even if you move off the grid and into a shack in the woods.
The best line of defense in a world full of hackers, scammers, and corporations playing fast and loose with your personal data is to be a more difficult mark than the average consumer. Using two-factor authentication and a password manager are two big steps you can take in that direction. Those moves will make you safer, at least until we have better options, like ultrasonic fingerprint mapping, which uses our heartbeat rhythms for authentication.