In five years, your Google accounts will be way more secure than they are today. The company recently revealed a five-year roadmap detailing stronger, more complex authentication methods that’ll make it harder to gain unauthorized entry into your accounts.

“We will change sign-in to a once-per-device action and make it higher friction, not lower friction, for all users,” Google group product manager for identity, Eric Sachs, told ZDNet.”We don’t mind making it painful for users to sign into their device if they only have to do it once.”
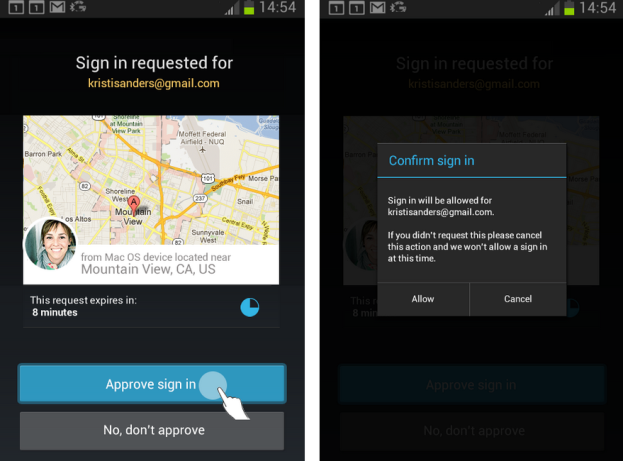
Google will also eventually switch on two-step authentication by default to add another layer of security on top of the log-in process.
The company released a similar plan back in 2008, but Google has had to rethink everything on account of smartphones becoming so advanced and popular. Sachs admitted Google didn’t see the high rate of smartphone adoption coming, hence the new roadmap. In addition to a more stringent login process on your main device, Google also has plans to make accessing your accounts on a second device more intricate. You’ll most likely need your first phone or tablet on hand to authenticate your second one via NFC or a similar technology.
These are but a few of the things Google hopes to accomplish within five years in an effort to combat increasingly more frequent security breaches. To read the full roadmap, check out the lengthy document the company has published.

