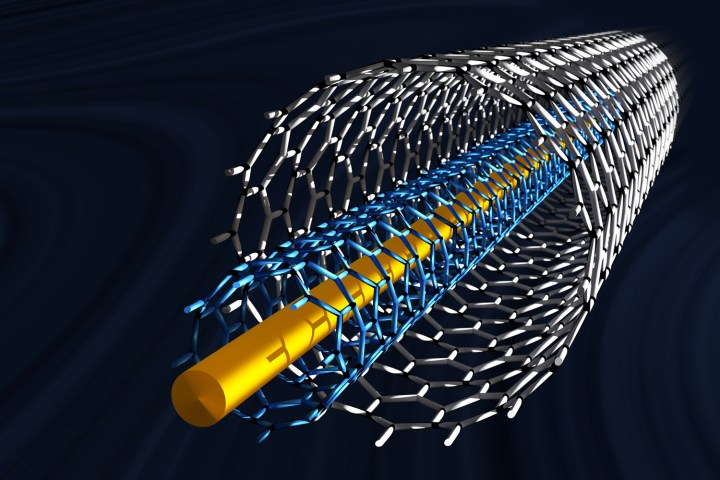
But a team of researchers has leveraged the aforementioned obstructions to work in their favor. Instead of using carbon nanotubes to create a processor, the group discovered that they could produce cryptographic information by wiring up a section of a chip at random. This randomness lets the nanotubes serve as a means of on-chip, hardware-based encryption.
This is all carried out using a detergent called SDS, which pushes the nanotubes to a part of the chip marked with a positively charged substrate. Notably, this can only be achieved by varying the spacing of the elements in question, thereby preventing a disproportion between attraction and repulsion, and effectively making it possible to handpick just how many locations become populated with carbon nanotubes.
In manually setting the conditions, it’s possible to set a maximum percentage of gates occupied by a nanotube, but not possible to know ahead of time which ones will be occupied. That’s why it’s secure to use this technique as a means of generating an encryption key.
To demonstrate their breakthrough, the researchers built a 64-bit prototype and proved its ability to regularly generate similar keys while also confirming that the process was unaffected by environmental noise. Likewise, the researchers confirmed that over 99 percent of the time, the hardware will generate keys with more than half of their bits completely discernible from one another.
The researches say this technique is even impervious to any attempt to remove the chip from a device to read data bit-by-bit. Since the encryption system comes down to the hardware rather than the software, the processing chip itself would need to be imaged. Although theoretically possible, the researchers say that the chip’s construction makes any attempt to do so likely to destroy the chip entirely, and thus destroy the protected data.
“High-resolution imaging techniques such as electron microscope imaging cannot be used to analyse the bit information,” explain the authors in their write-up. “As the chip de-layering processes (to expose [the nanotubes]) involve harsh plasma etching.”
In doing so, it would close the one remaining loophole that might be used to attack a device with encryption, such as an iPhone, render devices truly secure against any known attack.


