- Home
- Computing
Computing
About
News, reviews, and discussion about desktop PCs, laptops, and everything else in the world of computing, including in-depth buying guides and daily videos.

How to delete a Discord server on desktop and mobile




Best Squarespace deals: Save on domains, web builder, and more

Save $150 on a lifetime license for Microsoft Office for PC

You’re going to hate the latest change to Windows 11

The best resume templates for Google Docs


This popular Dell business laptop is discounted from $849 to $579

Save $100 on this Netgear mesh Wi-Fi system at Crutchfield

ExpressVPN Deals: Save 49% when you sign up today

Gigabyte just confirmed AMD’s Ryzen 9000 CPUs
Even the new mid-tier Snapdragon X Plus beats Apple’s M3
4 CPUs you should buy instead of the Ryzen 7 7800X3D

This Alienware gaming PC with an RTX 4090, 64GB of RAM is $1,000 off

The 10 best monitors for 2024: tested and reviewed

The Razer Blade RTX 40 series gaming laptops are on sale right now

Surface Pro 10: all the major changes rumored for the new model

Meta Smart Glasses just got the AI upgrade I’ve been waiting for

How to check your CPU temperature

Snag this 34-inch LG Curved Ultrawide WQHD monitor for $249

Save $300 on this HP desktop PC with an RTX 3060, 1TB SSD

Razer made the best gaming mouse even better

A Redditor ‘didn’t know’ about the Steam Deck, so they built their own

Windows 11 Home usually costs $139 — but it’s only $30 today

5 web browsers you should use instead of Google Chrome or Edge
Computing News
Laptops
Computing Reviews
Nvidia
Have you had enough of Discord for a while? We get it. It can be a little exhausting to say the least, especially if you’re running a jam-packed server, filled with multimedia and messages. Fortunately, if you’re in the mood to take a break, it’s not too hard to delete your Discord server.
(function() { const el = document.getElementById('h-662a7172e3f1d'); const list = el.querySelector('.b-meta-table__list'); const listModifier = 'b-meta-table__list--long'; const moreItems = (el.querySelectorAll('.b-meta-table__list-item')).length - 4; const btn = el.querySelector('.b-meta-table__button'); const additionalBtnClass = 'b-meta-table__button--active'; if (btn) { btn.addEventListener('click', function(e) { if (list.classList.contains(listModifier)) { list.classList.remove(listModifier); btn.classList.add(additionalBtnClass); btn.innerHTML = JSON.parse(decodeURIComponent('%22Show%20less%22')); } else { btn.innerHTML = moreItems === 1 ? 'Show 1 more item' : 'Show ' + moreItems + ' more items'; btn.classList.remove(additionalBtnClass); list.classList.add(listModifier); } }); } })();Of course, we would never leave you in the weeds. So to that end, we’ve put together this step-by-step guide to help you pull down your Discord server in no time at all.
Using the server settings
Step 1: You’ll need to open the Discord server you created by selecting it within the app itself.
Step 2: Once it’s been opened, select the name of the server situated at the top of Discord, adjacent to the Home button.
Step 3: Select the Server settings field.
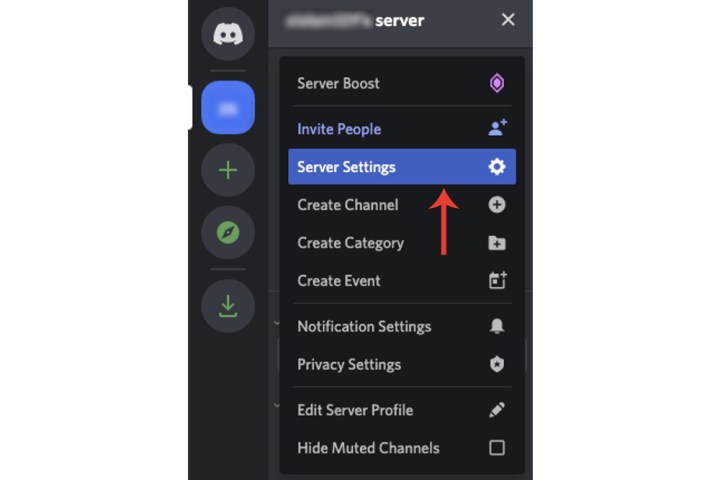
Step 4: Select Delete server adjacent to the bin icon.

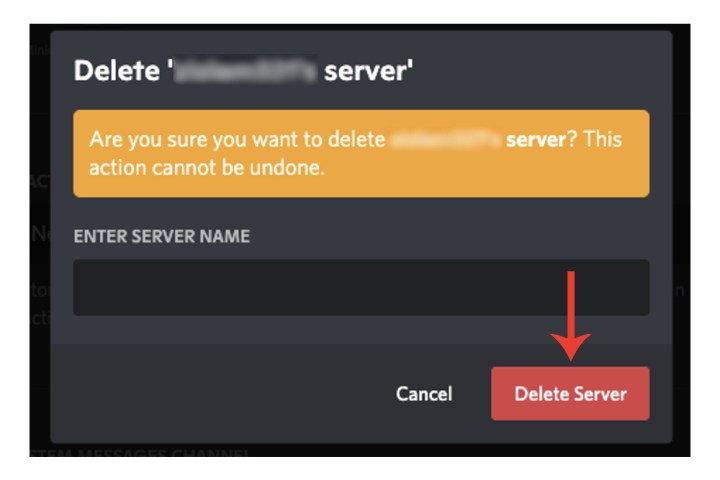
Step 5: Discord will require you to enter the name of your server.
Step 6: Select the Delete server button.
Although you can recover a deleted account on Discord, the platform does not provide the same option for deleting a server. Once you proceed with deleting your server, it will be permanently removed from Discord’s systems. As such, make sure you save anything that may be valuable within your server before you delete it.
How do I delete a server on Discord on the iPhone?
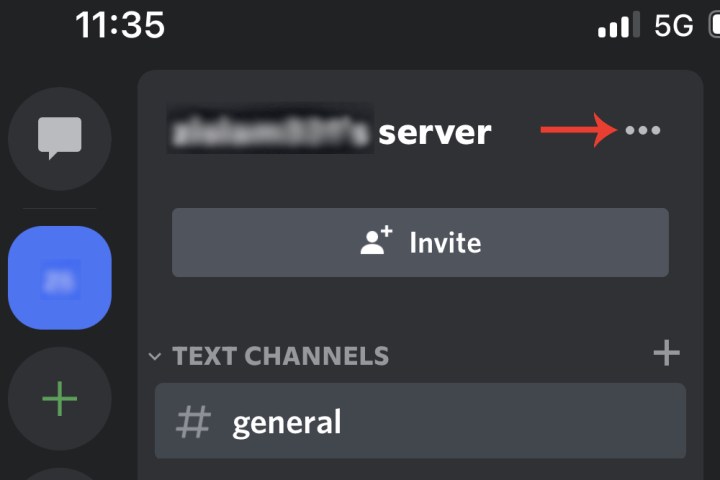
Step 1: Open the Discord app on the iPhone, click the server you want to delete from the side, and then on the top right, select the Three dots adjacent to the server name.
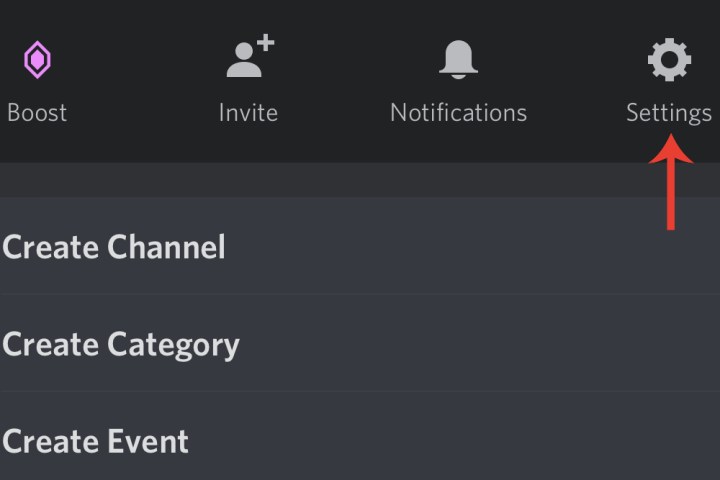
Step 2: Click Settings > Overview.
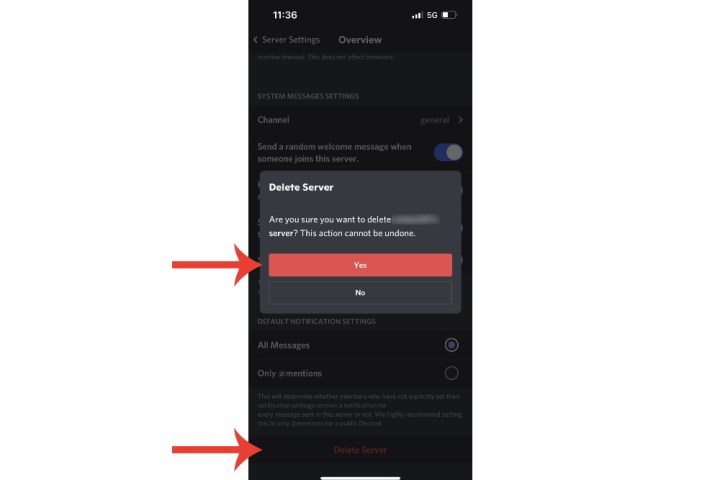
Step 3: Scroll down to the bottom and click Delete server. A message will ask you to confirm the deletion. Click Yes. You won’t have to type the server name.
How do I delete a Discord server without admin access?
If you don’t have admin control of a server (which you would if you created it or ownership was transferred to you), then you won’t be able to delete it.
However, if you feel the server itself is illegal, dangerous, contains spam, etc., you could report it to Discord, which will launch its own investigation and may decide to delete it.
You can do so via Discord’s official submit a request page, where you’ll be able to provide evidence via screenshots. You can also include a link to specific messages that are relevant in your report.
If you decide to delete your Discord account completely, check out our guide on how to do so.