- Home
- Computing
Computing
About
News, reviews, and discussion about desktop PCs, laptops, and everything else in the world of computing, including in-depth buying guides and daily videos.
How to delete your Gmail account (and what you need to know)




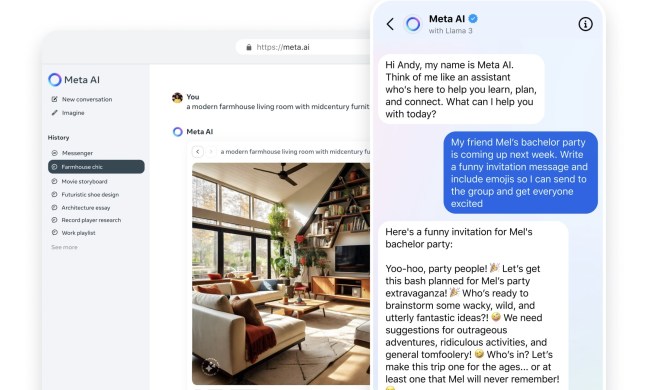
Why Llama 3 is changing everything in the world of AI

How to delete or hide chats in Microsoft Teams

How to customize mouse gestures on Mac

How to delete a Discord server on desktop and mobile


The Asus ROG Ally just got a game-changing update

How to easily connect any laptop to a TV

This laptop beats the MacBook Air in every way but one

This ultra-portable Lenovo 2-in-1 laptop is discounted from $649 to $199

How to connect a keyboard and mouse to the Steam Deck

This HP laptop is discounted from $519 to $279

How to choose the best RAM for your PC in 2024

The next big Windows 11 update has a new hardware requirement
Squarespace free trial: Build and host your website for free

The best web browsers for 2024

Microsoft Word free trial: Get a month of service for free

Best Squarespace deals: Save on domains, web builder, and more

Save $150 on a lifetime license for Microsoft Office for PC

You’re going to hate the latest change to Windows 11

The best resume templates for Google Docs

This popular Dell business laptop is discounted from $849 to $579

Save $100 on this Netgear mesh Wi-Fi system at Crutchfield

ExpressVPN Deals: Save 49% when you sign up today
Computing News
Laptops
Computing Reviews
Nvidia
Is it time to part ways with your Gmail account? Whether you’re moving onto greener email pastures, or you want to start fresh with a new Gmail address, deleting your old Gmail account is something anyone can do. Of course, we’re not just going to bid you farewell without a guide all our own. If you need to delete your Gmail account, we hope these step-by-step instructions will make the process even easier.
(function() { const el = document.getElementById('h-662adb8267c8d'); const list = el.querySelector('.b-meta-table__list'); const listModifier = 'b-meta-table__list--long'; const moreItems = (el.querySelectorAll('.b-meta-table__list-item')).length - 4; const btn = el.querySelector('.b-meta-table__button'); const additionalBtnClass = 'b-meta-table__button--active'; if (btn) { btn.addEventListener('click', function(e) { if (list.classList.contains(listModifier)) { list.classList.remove(listModifier); btn.classList.add(additionalBtnClass); btn.innerHTML = JSON.parse(decodeURIComponent('%22Show%20less%22')); } else { btn.innerHTML = moreItems === 1 ? 'Show 1 more item' : 'Show ' + moreItems + ' more items'; btn.classList.remove(additionalBtnClass); list.classList.add(listModifier); } }); } })();How to delete your Gmail account
You can head to your Google account any time by navigating to your profile picture on Gmail and selecting Manage your Google Account. Or you can get to your account immediately by following this handy link. If you aren’t currently signed in, you will need to sign in to your Google Account.
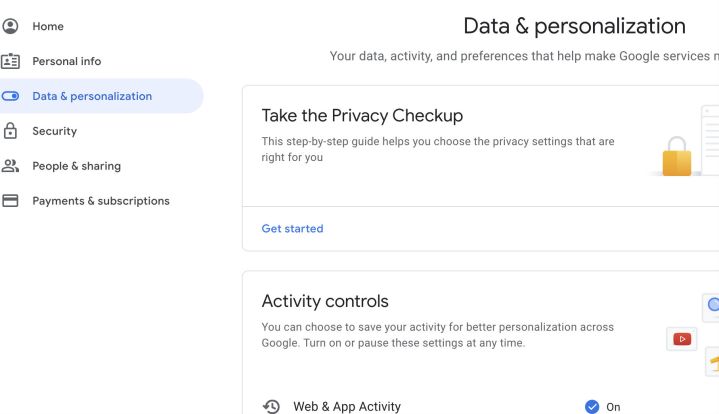
Step 1: Once on your Google account, look at the left-hand menu and select Data and personalization. This is the section that controls privacy, data storage, and many important settings, including the ability to delete your Gmail account.
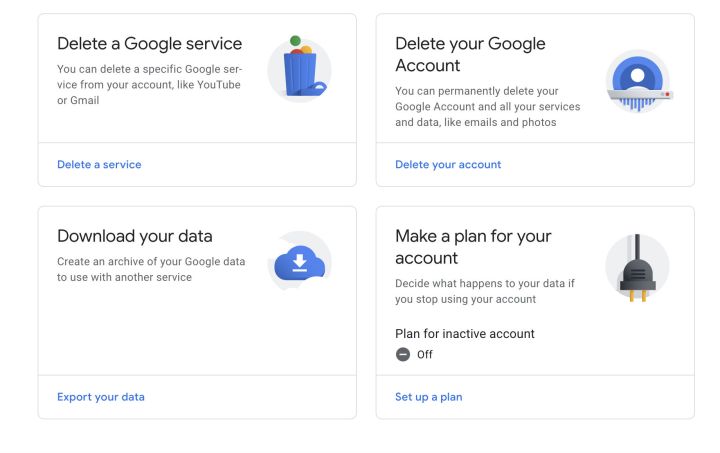
Step 2: Scroll down until you find the section that says Download, delete, or make a plan for your data. Here you will want to select the option that says Delete a service or your account. Here is where you can delete anything you’ve signed up for with Google, including your Gmail account.
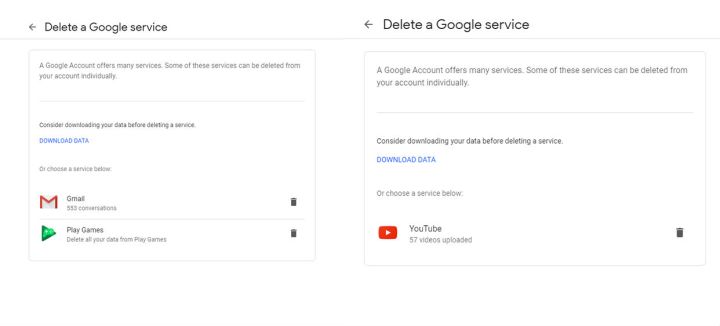
Step 3: On the following screen, select Delete a Google service to proceed — you can also choose to delete your entire Google account here, but this isn’t necessary if you just want to get rid of Gmail. You can also choose what to do with your data if you are thinking about not using your Google Account anymore, preparing for what happens if you die, and so on.
At this point, Google will ask you to log in again with your account password, so be prepared for providing that data.
At this point, you can choose to download valuable data to save it after you delete your account, which may be a good idea if you have important Gmail conversations.
Step 4: Now you’ll see all the Google services that you currently have active. Look for Gmail, and select the trash can icon to begin the process of deleting it.
Google will now require you to enter a new email address for your Google account login options. This new email address cannot be a Gmail address. If you haven’t already set up a new email account elsewhere…this is the time to do it. If you’ve already entered a secondary email address for your Google account, Google will automatically select this email to use instead.
Google will now send you a confirmation email at that address. Wait until you receive, then open the email and click the link to permanently delete your Gmail account. Google will give you a last warning before you complete the process — and then you’re done!
Step 5: Remember, you can make more detailed plans for your account inactivity by going to Delete a service or your account and choosing Make a plan for your account. This can help you if you decide to stop using Google or are unable to, but it’s also a good way to generally control your data and choose if you want to share it with anyone in case of an emergency. You can also use these tools to set your Google account to automatically delete itself if it isn’t used for a certain period of time.
If you’ve saved emails from Gmail for offline use or use Gmail offline in any way, then your browser has probably saved some problematic info. To avoid these problems, delete your browser cache and clear the cookies in your browser to make sure any data stored from your Gmail is gone.
Remember that if you have Gmail linked to an email app on your phone or other device, you will also need to switch it to a new email address and service.
A note on deleting an email address
If you’ve been using your email for a long time, remember that you have probably used it to register for services and sign into everything from bill pay features to one-hit-wonder apps that you no longer use. When you get rid of your Gmail account, you will no longer receive updates or reminders from any of these accounts. Some accounts may no longer function if they cannot find a responsive email address, which means you may have to change your account info or create a new account. In other words, get ready for some cleanup work after your old email is gone.