The Ware Report, an 82 page document written by a team including computer science legend Willis Ware, was recently added to The National Security Archives at George Washington University. The document, declassified in 1975, outlined what were then largely theoretical weaknesses in networks. They’re all-too-real now.
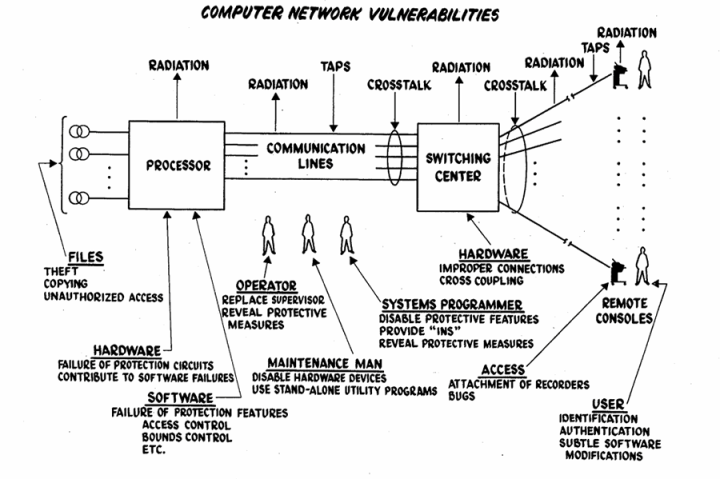
Ars Technica IT editor Sean Gallagher argued today that most major hacks and attacks in the modern could have been prevented, if only the report’s lessons were taken seriously. Among the potential system weaknesses outlined are:
- Exposure or destruction of data caused by system failure or administrative mistakes.
- Attackers exploiting weaknesses in user credentials (ie, weak passwords) or software vulnerabilities (ie, exploits).
- “Passive subversion”, collecting network traffic in bulk as it moves across the network, (eg., the NSA’s bulk collection of data).
From ransomware to phishing to the Sony hacks, most security problems we face today were outlined in this document, put together for the Department Of Defense as they contemplating building ARPAnet, the computer network that would eventually evolve into the Internet we know today.
“Providing satisfactory security controls in a computer system is in itself a system design problem,” wrote Ware in a memo summarizing his report. “A combination of hardware, software, communication, physical, personnel and administrative-procedural safeguards is required for comprehensive security. In particular, software safeguards alone are not sufficient.”
It was true then, and it’s now — cybersecurity is complicated, especially when a computer is connected to a worldwide network. No one tool can keep you secure. Firewalls and antivirus won’t protect someone from phishing, which exploits human nature to access a system. At the same time, a well-trained user can still end up infected if security patches aren’t fast enough. Security isn’t any one thing. It’s a combination of several, and every organization needs to take that seriously.
Ware and his co-authors didn’t precisely predict today’s state of cybersecurity, but the lessons he offered the Defense Department are still worth reading today.


