 Sony just can’t catch a break. Yesterday, SonyMusic.gr was infiltrated by hackers via an SQL injection tool. The unsophisticated attack compromised the site’s user database, leaking name, e-mails, and addresses of those registered.
Sony just can’t catch a break. Yesterday, SonyMusic.gr was infiltrated by hackers via an SQL injection tool. The unsophisticated attack compromised the site’s user database, leaking name, e-mails, and addresses of those registered.
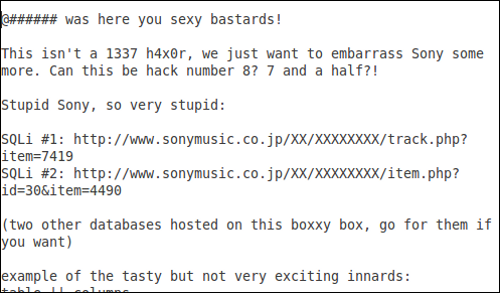
Today, Sony’s Japan music site has suffered the same fate. Sophos, which discovered yesterday’s hack, found similar damage to SonyMusic.co.jp. According to Chester Wisniewski via the site’s Naked Security IT blog, Hacker News first found the affected web pages. As reported yesterday, an SQL injection was used to access the site’s contents, including its user database. Fortunately, this instance did not concede as much user information, and names, passwords, and other “personally identifiable information” are believed to be safe. But it’s still unknown what exactly hackers were able to access. Wisniewski says it is possible they could have inserted malicious code that would then affect the site’s visitors.
What’s most distressing about this latest chapter in Sony’s security saga is that it is once more proving the company’s complete negligence. These particular hacks are only utilizing Sony’s own security flaws and exposing them. One of the
Even if Lulz Security is behind the attack and has no interest in stealing customer information, the scale of Sony’s mounting security failures is enough to keep subscribers anxious. Of course it’s also enough to see many of them drop Sony services altogether.
[UPDATE]
After earlier speculation this morning, Sony Ericsson Canada has confirmed to IDG News Service it has been hacked. Hacker News reported that a group of Lebanese hackers is behind this attack and that they also used an SQL injection. It appears that the online store and customer database was accessed and while credit card information is reportedly safe, first name, last name, e-mail addresses and the hash of encrypted passwords were breached.


