At South by Southwest 2014 on Monday, Edward Snowden said the best way – perhaps the only way – to prevent mass government surveillance is through the use of widespread end-to-end encryption. Slamming the door on the NSA with technology, in other words, rather than waiting for the legal process to do it for us.
“The actual collection problem doesn’t seem to be a bottleneck for the NSA, and that’s because the so many of the services that we’re relying on are not secure by default,” explained ACLU Principal Technologist Chris Soghoian, Snowden’s fellow SXSW event speaker. “We need to lock things down,” he said.
He’s right, of course. But with a slew of options for locking things down already available, the bigger issue may simply be getting people to use them. I wonder if words like “privacy” and “encryption” are holding them back more than helping.
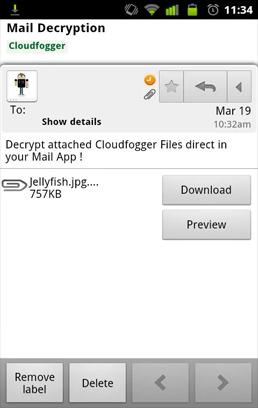
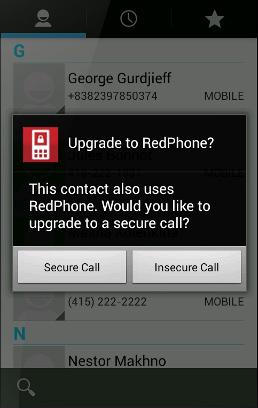
There’s Mailvelope browser plugin for encrypted emails,Cloudfogger for securely using Dropbox and other cloud storage services (or SpiderOak if you want to avoid the mainstream cloud options altogether), Cryptocat and Telegram for secure text messaging through your Web browser or iPhone, and Whisper Systems (which Snowden name-dropped at SXSW) whose RedPhone app for Android enables encrypted calls. Do any of you use any of these? Have you even heard of these? I’d bet hard cash that the percentage of who can say yes is incredibly low.
One problem with these communication services is that they require not just you but everyone you speak with to also use the service, in order for it to be effective. In the case of Cryptocat, which just launched for iPhone last week, for example, there’s often not anyone else to talk to. Not a single one of my friends or family thought Cryptocat was worth the (free) download. And the app currently has just six reviews in the iTunes App Store.
Then there is, of course, TOR – the routing network that encrypts user traffic, bounces it around through a jumble of IP addresses, and makes it extremely difficult (but not impossible) for whomever might be watching you to do so effectively. But as Ben Wizner, Snowden’s attorney and director of the ACLU Speech, Privacy & Technology Project who moderated the Snowden SXSW event, said, “Using Tor … I feel like I need new IT support in my office just to be able to do this work.”
Tor, like so many other encryption services that actually protect privacy and security, is ugly, slow, and thus seems like an unnecessary burden for everyday Web browsing and communications. As Soghoian said, “we should understand that most regular people are not going to go out and download an obscure encryption app. Most people are going to use the tools that they already have. That means that they are going to be using Facebook or Google or Skype.”
We need secure communications tools that pretend to be nothing of the sort.
The solution, Soghoian believes, is to change the business model.
“I think we are slowly getting to the point where telling your customers, ‘Hey, $5 a month for encrypted communications, no one can watch you.’ I think that is something that many consumers may be willing to pay for,” he said.
Perhaps. WhatsApp, with its nearly half-billion users and $19 billion from Facebook, proves that we are willing to pay for services that at least tip their hat to privacy – as long as the price is around $1 per year. WhatsApp also proves that, despite what I found with Cryptocat and similar privacy-focused services, people are willing to switch to closed systems in order to communicate with one another. Were WhatsApp to provide end-to-end encryption then we’d be a whole lot closer to the private future Snowden envisions.
What we are not willing to pay for is privacy alone. We need another reason to use a service besides it being secure. In fact, considering 55 percent of Americans told Washington Post-ABC News pollsters in November that they believe Snowden did the “wrong thing” by exposing the NSA’s dragnet ways, putting surveillance-blocking at the forefront of your marketing message may do more harm than good.

The answer, then, is to build communication services that include privacy features but don’t tout them as the most important thing. We need secure communications tools that pretend to be nothing of the sort.
For those who care about privacy above all else, that may seem like an idiotic thing to say. But if you’re anything like me, you leave your car doors unlocked when you feel like it’s safe to do so. And you don’t want to actively hide everything you say behind encryption walls when you know you’re not saying anything incriminating. Doing so feels a bit skeevy and odd – illicit in and of itself. And besides, why be more secure than necessary?
Snowden, Soghoian, and the rest of the privacy advocates of this world are right to warn us about the pervasive surveillance of the world’s innocent people. Those of us who hate the idea of being watched by the government for no good reason are rightly upset. And encryption is, I believe, the right way to go about solving our spying woes. But it’s important for the developers who will help solve this problem to remember: For most of us, the reason we don’t take the time to learn how encryption works is because we simply don’t want to think about it at all.