That is probably not terribly fair — anyone can be tricked into plugging in such devices, given that they are designed to look just like any other flash drive. And there is little you can do to protect yourself against them, which is something a new hardware firewall called USG is intended to help prevent, Hackaday reports.
The reason malware-infected USB flash drives are so dangerous is that devices using attacks like BadUSB inject their malicious code directly into the USB driver software that enables a PC to connect to a USB device. The code is executed by the USB device’s own microprocessor, meaning there is no virus file being accessed on the PC that antivirus software can recognize and protect against.
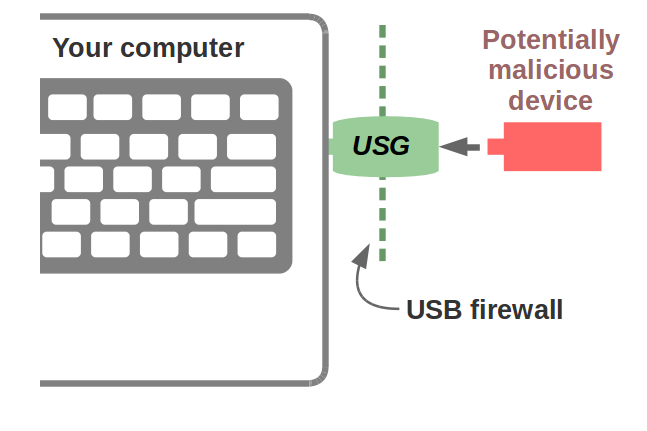
The USG device created by engineer Robert Fisk sits in between the PC’s USB port and any device that is going to be plugged in, inserting an SPI hardware firewall to isolate any bad USB device. Because the firmware of the USG device is completely open, anyone with the technical know-how can dig into it and verify that it can be trusted — something that’s just not possible with the typical USB flash drive.
According to some sources, even factory-fresh USB flash drives can’t be assumed free of malware, backdoors, and other nefarious purposes, and so a device like the USG could one day be more than just a luxury of the paranoid. Fisk provides details on how to build your own USG device, along with information on how and why it works. He also sells a version that is more professional in appearance for $60, in case you don’t have the time or technical inclination to build your own.
Updated on 3-6-2017 by Mark Coppock: Clarified that the USG is an SPI hardware firewall and updated pricing information.



