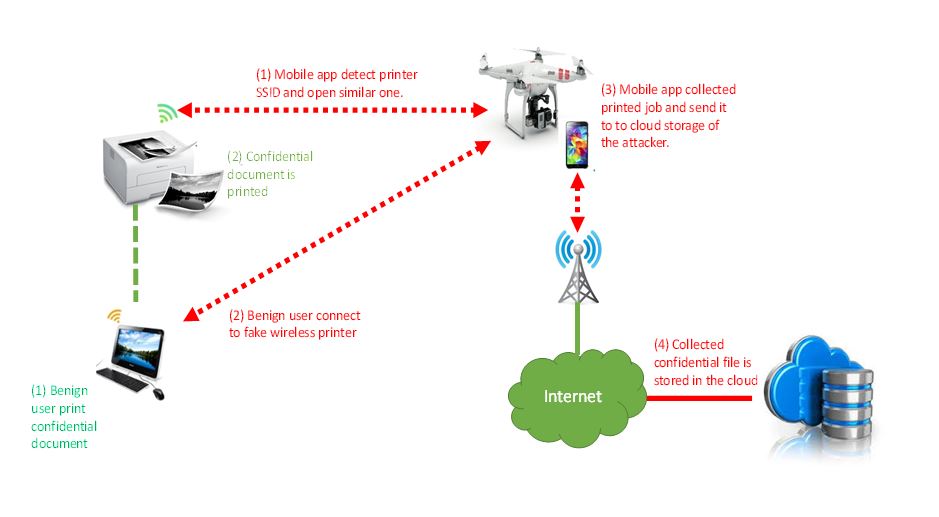
The iTrust system was designed as an inexpensive way for companies to test the security of their Wi-Fi networks, but as the researchers demonstrated, it can also be used for nefarious purposes. It uses drones to transport a smartphone to an area where a wireless network with wireless printers is located. Unlike notebook-based detection systems that require building access, drones can fly outside a fly outside a skyscraper and find vulnerable networks with minimal interference. The system targets wireless printers because they often The weak link in a company’s wireless network. Wireless printers are typically supplied with the Wi-Fi connection open by default, and many companies forget to close this hole when they add the device to their Wi-Fi networks. This open connection potentially provides an access point for outsiders to connect to a network and steal a company’s sensitive data.
The system designed by iTrust uses a consumer DJI drone and a Samsung smartphone loaded with apps designed by the researchers to test a company’s wireless network. One app, Cybersecurity Patrol, scans for open Wi-Fi printers and alerts a user if a vulnerable device is found. The second app also scans for open Wi-Fi devices but goes a step further by trying to hack into the network. It attempts to access the network by creating a fake access point that mimics the wireless printer. If successful, the smartphone-based fake printer can intercept documents sent to the office printer within seconds and reroute them to a Dropbox account using the phone’s cellular connection.
Hacking the network and stealing the printer documents is not a trivial undertaking and requires the researchers to root the Samsung phone and install Debian Linux on the handset. They then use python to write an app to emulate an HP6830 wireless printer after they reverse engineered the software from the actual printer. They also need to be within a 26-meter radius of the network, making it likely a drone would be spotted hovering outside an office building.
Though it may be challenging to use as an attack vector, the drone system is effective for scanning and detecting open networks. Users only need to install the Cybersecurity Patrol app on a phone and send it upwards via a drone. It also can be attached to a robotic vacuum cleaner, which will scan for vulnerable networks while it cleans a company’s floors.