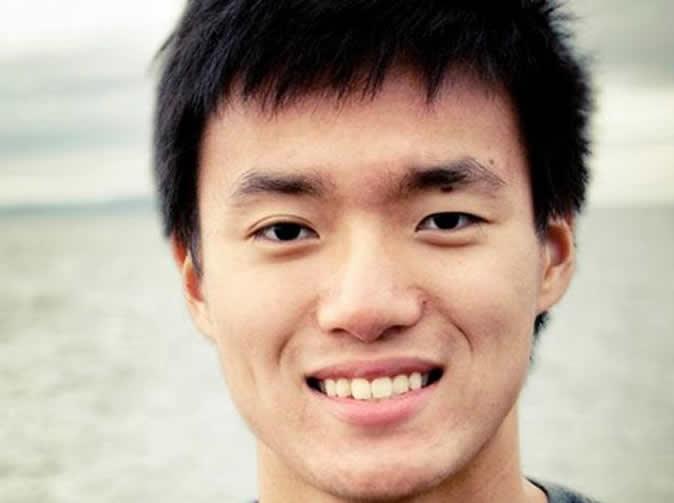
Harvard University went on lockdown Monday after administrators received emails claiming bomb threats against four campus buildings. Turns out, there were no bombs – thankfully. Instead, the threats were allegedly sent out by Harvard sophomore Eldo Kim, who The Crimson reports was apparently trying to avoid taking a final exam.
As PJ Vogt at On The Media’s TLDR blog points out, the FBI was able to identify Kim despite the fact that he sent the emails after connecting to Tor, a network that anonymizes users’ IP addresses to make it look like online activity is coming from somewhere else.
Seeing as Tor is often used to access the “deep Web” – content and websites not included in “clear Web” search results from Google or other search engines – where many nefarious communities reside, the network’s ability (or inability) to keep its users anonymous is a hot talking point.
Kim’s problem was not with Tor, but with the way he apparently used it. As the FBI affidavit explains (pdf), Harvard’s IT staff “was able to determine that, in the several hours leading up to the receipt of the e-mail messages described above, Eldo Kim accessed Tor using Harvard’s wireless network.” The administrators were probably able to pinpoint Kim because he was likely one of the few people accessing Tor on Harvard’s Wi-Fi, if not the only one.
Which brings us to this tale’s takeaway: Just because Tor can anonymize your online actives and make them difficult to track doesn’t mean it will – especially not when you’re using a monitored Internet connection. There are ways to use Tor to remain nearly untraceable, as this in-depth slideshow details. Kim, it would seem, did none of it.
Because of this oversight, Kim has been arrested and faces up to five years in prison for his bomb threat hoax. We all know finals suck – but wouldn’t it be easier to take the test?


