Google’s Project Zero team released a report identifying another security flaw in Microsoft Edge. The team traditionally provides 90 days for developers to fix the uncovered issue(s) and exposes said issue(s) if they are not resolved within that timeframe. That means Microsoft didn’t respond to the team’s initial bug report, thus Project Zero is now coming forward with its findings.
But Microsoft isn’t simply ignoring the report. The company deems the issue as “important” rather than “critical” because hackers can’t remotely take advantage of the Microsoft Edge security hole. Instead, they must execute code locally on the target PC using a normal privilege level. But the researcher who discovered the vulnerability deems it as “high severity” given it’s still easy to exploit despite the need for local device access.
As for the actual problem, it provides hackers with administrator privileges on the target PC. That essentially means they can do anything on the device: Install programs, delete files, and so on. Getting administrator privileges through the vulnerability starts with the way a “hard-linked” file receives a security descriptor and is moved to a new destination. Once in the new folder, Windows 10 changes the file’s security descriptor to match the security settings of the current folder.
That said, if the hard-linked file was originally set to read-only, the flaw allows anyone on the network to edit that file after it’s moved to the new directory. That is a simplified explanation and is apparently only a problem on Windows 10. The Project Zero team successfully exploited the security flaw on Windows 10 version 1709.
The issue is one of two reported by the Project Zero team. The first problem, Issue 1427, received a fix on February 13, whereas the issue listed in the public report published on Tuesday, February 20, (1428) was not. The Proof of Concept consists of software compiled in C++ executing as a normal user to create a file in the Windows folder using the “SvcMoveFileInheritSecurity” method.
The issue Microsoft did fix is listed as CVE-2018-0826. According to the filing, Windows Storage Services “allows an elevation of privilege vulnerability due to the way objects are handled in memory.” It applies to Windows 10 versions 1511, 1607, 1703, and 1709 along with Windows Server 2016 and Windows Server version 1709.
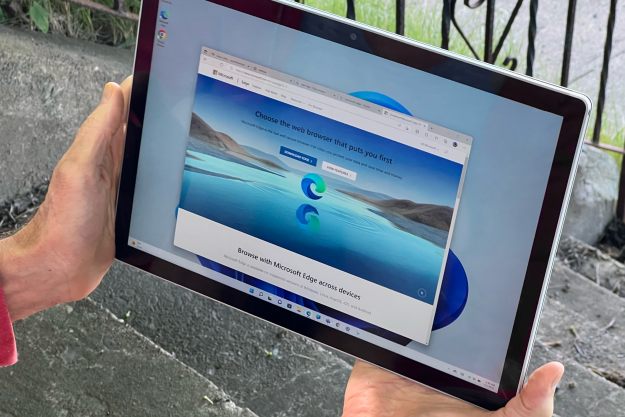
Google’s Project Zero team disclosed another vulnerability earlier this week that Microsoft has yet to fix. Originally disclosed to the company in November, the bug resides in Microsoft Edge and centers on a compiler for JavaScript. Hackers can compromise the browser by predicting the path of the compiling process. Unfortunately, Microsoft couldn’t provide a fix before the 90-day deadline.
“The fix is more complex than initially anticipated, and it is very likely that we will not be able to meet the February release deadline due to these memory management issues,” the Microsoft Security Research Center stated. “The team is positive that this will be ready to ship on March 13th.”
Editors' Recommendations
- 5 web browsers you should use instead of Google Chrome or Edge
- Microsoft Edge is slowly becoming the go-to browser for PC gamers
- These 2 new Edge features are making Chrome look outdated
- Microsoft is already expanding Bing Chat to Skype and phones
- 5 features I’m itching to try in Microsoft’s ChatGPT-powered Edge Browser