“Microsoft is aware of a security feature bypass vulnerability in Secure Channel that affects all supported releases of Microsoft Windows,” the company wrote. “We are actively working with partners in our Microsoft Active Protections Program to provide information that they can use to provide broader protections to customers.”
Until the situation is under control, users are vulnerable to FREAK — but what is it exactly?
“FREAK” is short for Factoring attack on RSA-EXPORT Keys, according to ArsTechnica.com. The attacks are possible when a vulnerable user logs onto a vulnerable HTTPS-protected website using a device prone to being compromised. In this case, Windows computers fall into that category.
PCs and laptops aren’t the only products that could have a FREAK attack, however. Prior to the announcement from Microsoft, everything from iPhones to Android devices was thought to be susceptible to an attack.
During a FREAK attack, hackers watch the traffic passing between browsers and vulnerable servers. They can then inject malicious packets into the flow that cause the two parties to use a weak, 512-bit encryption key. With this weakness in place, hackers can collect some of the exchanged information using cloud-based computing.
Security researchers have found that out of 14 million HTTPS-protected websites, about 36 percent of them supported weak cipher, rendering them vulnerable to a FREAK attack. They note that companies including Google, Microsoft, and Apple have been slow to develop patches, which hints that FREAK attacks pose a low threat at the moment.
So don’t FREAK out just yet.
Editors' Recommendations
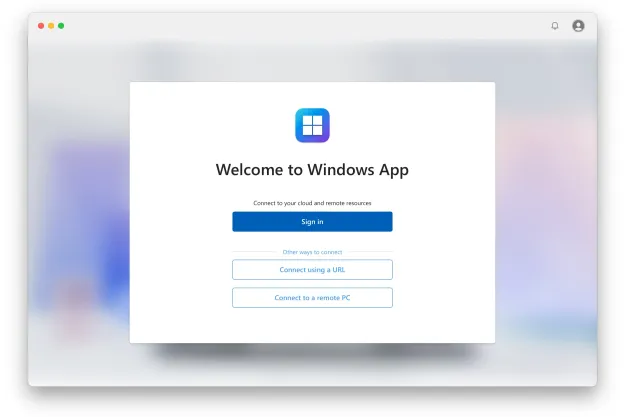
- The latest Windows update is breaking VPN connections
- Microsoft may fix the most frustrating thing about Windows updates
- How to remove a Microsoft account from Windows 11
- Microsoft plans to charge for Windows 10 updates in the future
- Windows may have a serious security problem on its hands