Originally, the Petya ransomware was not designed to lock down an entire PC for ransom, but just specific files. It must be downloaded by the user and remains on the victim’s PC to encrypt files and demand money for a decryption key. There are two other non-destructive variants of Petya as well including one called GoldenEye.
However, NotPetya surfaced weeks ago using the Petya ransomware as a weapon. It is capable of hopping from PC to PC across the network using an exploit called EternalBlue, which Microsoft actually patched prior to the outbreak. That means businesses affected by NotPetya had yet to upgrade their machines, leaving them open to attack.
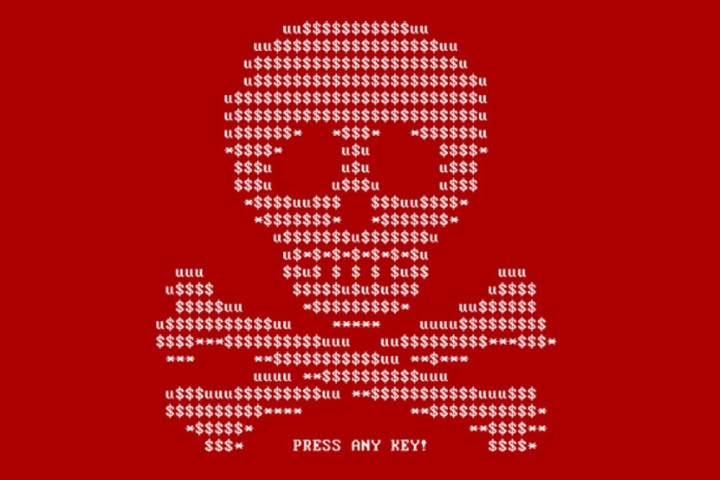
Once on a PC, NotPetya goes after the master boot record, thus overwriting the program that begins the Windows boot sequence. In turn, the table that keeps track of all files stored on the PC’s hard drive or solid-state disk is encrypted, making Windows unable to locate any file.
Once NotPetya encrypts a machine, it throws up a notice demanding money for the decryption key. In the early days, there was an account for receiving Bitcoin money from victims but that was quickly shut down. NotPetya continued to spread like wildfire with no way of regaining control of the infected machines.
However, on July 5, Janus Cybercrime Solutions jumped on Twitter and provided a link to a password-protected file located on a cloud-storage service. After cracking the password protection, researchers discovered it to be a master decryption key for the three versions of the Petya malware. They also realized that it has absolutely no effect on the current NotPetya epidemic.
Despite the key’s inability to unlock NotPetya-seized PCs, the master decryption key seemingly arrives too late. Petya and its variants mostly reined in 2016 and since then, victims have either paid the ransom or reformatted their PCs and reinstalled the software (which you should do from time to time anyway).
Even more, the master decryption key is not an out-of-the-box tool for anyone to use. Instead, it must be inserted into a stand-alone decrypter application. If anything, this master decryption key will help speed up current methods of recovering files encrypted by the Petya ransomware. This should come in handy for victims who may have replaced their PC’s entire storage unit and still have the drive on hand for future decryption.
Ultimately, this is bad news for NotPetya victims. Right now, the destruction-ware is seemingly locked down to the enterprise and business sectors, but that does not mean it will not jump ship into the mainstream waters. Make sure your version of Windows is up to date and follow our steps right here to prevent infection.


