In a lot of cases, the key to breaking encryption lies in the factoring of massive numbers. That system works because the equations are unable to be brute forced; the amount of iteration required would take thousands of years or more. That’s a limitation of our hardware, but MIT’s new quantum computer may be more than capable of overcoming that hurdle.
Quantum computing takes the familiar concepts of computing and turns them on their head. All data currently stored on systems is in bits of 1 or 0, on or off. Quantum computing doesn’t assume each bit is on or off, and instead the bits are constantly in a superstate of both on and off. This allows for some massively complex logic, which in turn makes it possible to calculate at speeds significantly quicker than any current supercomputer.
Which brings us to RSA. The security algorithm was first introduced in 1977, and ever since has been widely adopted as the standard for protecting data from chat messages to state secrets. It relies on two keys, one of which is public, one of which is private. Factoring the product of the two prime numbers decodes the message or data, and even modern supercomputers would take an immeasurably long amount of time to properly guess without knowing the private key.
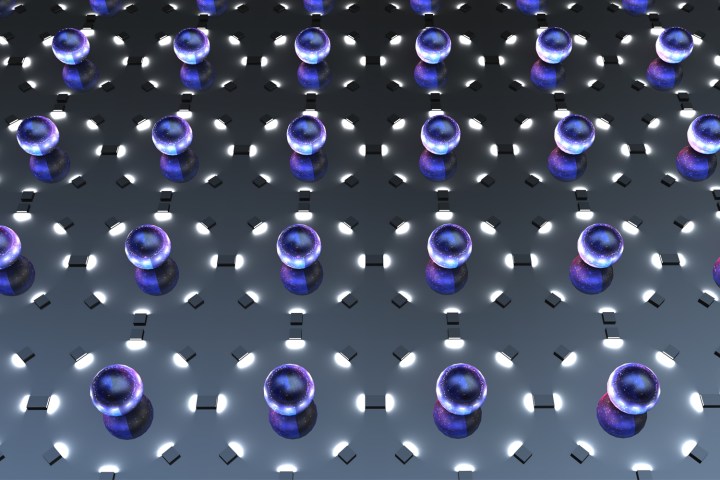
Like other quantum computers, MIT’s new five-atom system holds atoms in an ion trap, which allows the team to blast each with lasers and change or read its state. The system uses an older MIT algorithm to factor the numbers, which are up to 15 digits in length.
That’s a very impressive feat on its own, but the researchers also say the setup is modular, meaning it can scale to the workload. The technology is far from consumer, or even enterprise ready, which means the NSA still has some time to cover its tracks with new cryptography methods. Even with the complex equations, the system can’t crack RSA yet. But it does put in place the fundamentals needed to create a computer capable of it.
Editors' Recommendations
- Scientists just achieved a breakthrough in quantum computing
- IBM’s new 127-qubit processor is a major breakthrough in quantum computing
- We’re one step closer to a communication network based on quantum teleportation
- Microsoft’s plan to scrub carbon out of the atmosphere? Quantum computers
- Meet Silq: The first intuitive programming language for quantum computers


