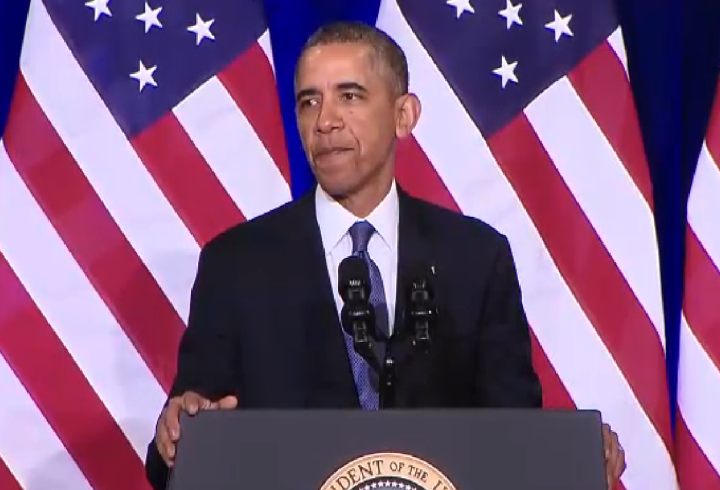
Seven months after the first disclosures from Edward Snowden went public, President Barack Obama announced Friday a list of “concrete and substantial reforms” to the way the United States conducts its surveillance operations. Changes include extending privacy protections to citizens in foreign countries, limiting the secrecy surrounding the use of National Security Letters, and reigning in the National Security Agency’s controversial bulk collection of telephone metadata.
NSA telephone metadata collection
The most significant changes for Americans concern the NSA’s telephone metadata collection program. Obama reiterated that the program, carried out under Section 215 of the PATRIOT Act, “does not involve the NSA examining the phone records of ordinary Americans” and has repeatedly been renewed by Congress. But he admitted that “ it has never been subject to vigorous public debate.”
“I am therefore ordering a transition that will end the Section 215 bulk metadata program as it currently exists, and establish a mechanism that preserves the capabilities we need without the government holding this bulk metadata,” he said.
Effective immediately, NSA analysts will no longer be permitted to “query” its database of telephone metatada without first receiving permission from the Foreign Intelligence Surveillance Court (FISC). And queries must now be limited to two steps from a “phone number associated with a terrorist organization,” Obama said. Earlier limits restricted queries to three steps from a targeted number, a jump many critics saw as overly broad.
Moreover, Obama said he may follow a presidential review board’s recommendation that the federal government turn over storage of telephone metadata to a third party, but admitted that doing so could cause new problems.
“The Review Group recommended that our current approach be replaced by one in which the providers or a third party retain the bulk records, with the government accessing information as needed. Both of these options pose difficult problems,” Obama said. “Relying solely on the records of multiple providers, for example, could require companies to alter their procedures in ways that raise new privacy concerns. On the other hand, any third party maintaining a single, consolidated database would be carrying out what is essentially a government function with more expense, more legal ambiguity, and a doubtful impact on public confidence that their privacy is being protected.”
Obama has asked intelligence officials and the attorney general to submit recommendations for how to properly transfer storage of the telephone metadata database to a third party before the collection program comes up for reauthorization on March 28.
National Security Letters
Obama also announced plans to limit the FBI’s use of National Security Letters, which often forbid recipients from disclosing that they had received the letter due to national security concerns.
“I have … directed the Attorney General to amend how we use National Security Letters so this secrecy will not be indefinite, and will terminate within a fixed time unless the government demonstrates a real need for further secrecy,” Obama said. He also plans to allow companies, like Google or Facebook, to “make public more information than ever before about the orders they have received to provide data to the government.”
Limit foreign intelligence gathering
Obama also issued a presidential directive that he says “will clearly prescribe what we do, and do not do, when it comes to our overseas surveillance.”
“In terms of our bulk collection of signals intelligence, US intelligence agencies will only use such data to meet specific security requirements: counter-intelligence; counter-terrorism; counter-proliferation; cyber-security; force protection for our troops and allies; and combating transnational crime, including sanctions evasion,” Obama said. “Moreover, I have directed that we take the unprecedented step of extending certain protections that we have for the American people to people overseas.”
Additional efforts will be taken to ensure that “unless there is a compelling national security purpose … we will not monitor the communications of heads of state and government of our close friends and allies.”
Review technological capabilities
Finally, Obama has ordered “a comprehensive review of big data and privacy” by a group that includes both government officials and “technologists and business leaders,” which will “look at how the challenges inherent in big data are being confronted by both the public and private sectors; whether we can forge international norms on how to manage this data; and how we can continue to promote the free flow of information in ways that are consistent with both privacy and security.”
More work to do
While Obama says that the reforms announced today “will point us in a new direction,” he admits that “more work will be needed in the future.”
“One thing I’m certain of: this debate will make us stronger. And I also know that in this time of change, the United States of America will have to lead,” Obama said. “It may seem sometimes that America is being held to a different standard, and the readiness of some to assume the worst motives by our government can be frustrating. No one expects China to have an open debate about their surveillance programs, or Russia to take the privacy concerns of citizens into account. But let us remember that we are held to a different standard precisely because we have been at the forefront in defending personal privacy and human dignity.”
What do you think of Obama’s efforts to curtail surveillance activities? Tell us down below.


