What did the DDoS attack do?
Typically, DDoS (Distributed Denial of Service) attacks are aimed at individual entities, like the one that Sony and several others suffered in 2014. When this happens, the company’s online services are disrupted, which in that case led to gamers being cut off from the Playstation Network and Xbox Live.
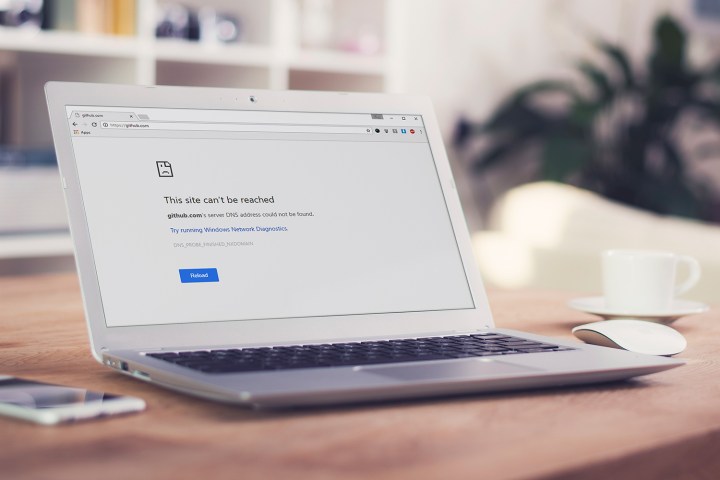
Friday’s attack targeted Dyn, a major provider of DNS services. Because Dyn’s DNS servers are responsible for translating domain names like www.digitaltrends.com into IP addresses, any company that was using Dyn to host their DNS became like a house on a street without its address displayed. The house was still there of course — if you already knew how to find it on your own, you could still get to it — but there was not way to look it up on Google Maps.
If a DDoS attack was aimed at all of the major DNS providers, it could bring the Internet to a stand-still.
If a DDoS attack were to be aimed at all of the major DNS providers simultaneously, from a botnet that was geographically diverse and had hundreds of millions of devices under its control, it could theoretically bring the majority of the Internet to a stand-still until the attack abated or the targeted companies could muster the resources to block it.
Since Friday, Dyn has disclosed that devices infected by the Mirai botnet were one source of traffic. According to Brian Krebs, a reporter who specializes in computer security, “Mirai scours the Web for IoT devices protected by little more than factory-default usernames and passwords, and then enlists the devices in attacks that hurl junk traffic at an online target until it can no longer accommodate legitimate visitors or users.” Krebs has also been victim of the Mirai botnet – it was used to attack his blog in September, and actually brought it down until Google’s Project Shield came to its defense.
Why should I be concerned?
Security experts believe the IoT devices used in this attack are of the consumer-facing variety. “Consumer products often have little security,” Ryan O’Leary, vice president, Threat Research Center, WhiteHat Security, tells Digital Trends via email, “and the users who set these up have little security knowledge.”

O’Leary says these two factors combine to make “a very easy attack surface.” Wi-Fi security cameras, thermostats, and even garage door openers can all potentially be turned into zombies and added to a botnet, awaiting the instructions that could have contributed to Friday’s havoc.
These devices aren’t powerful, and individually, they’re not much threat. But hundreds of millions of them exist. When bundled together, they turn into the most powerful weapon on the Internet.
If you’re beginning to wonder whether any of your IoT devices could have been involved, good — that’s exactly what we need to be asking ourselves.
OK, now what?
So what can you do, exactly? For starters, if you do not have a password on your Wi-Fi router, or you’re using the default password, change it immediately and select WPA2 as the security mode, not the older WPA or WEP.
“This is the new standard of security,” O’Leary says, and points out that while you’re at it, you should also disable WPS, or Wi-Fi Protected Setup: “This feature has significant security vulnerabilities.” Making these changes ensures that your home network isn’t welcoming intruders with open arms — a good idea even if you don’t own a single IoT device.
But it doesn’t stop there. Because your home network is connected to the Internet at large, malicious entities like the Mirai botnet can probe your connected devices remotely.
Belkin, maker of the popular WeMo brand of IoT devices, says it’s very aware of this threat. In an emailed statement, the company said, “Wemo is designed so that our devices are not discoverable from anywhere on the Internet outside the home’s Local Area Network,” and it also points out that its installation procedure doesn’t modify a user’s port settings on their Wi-Fi router (open ports are yet another avenue for attack). If you’re unsure whether your router has open ports, there are a number of free tools like yougetsignal.com that can give you a report in less than a minute.
The next step is to make sure your existing IoT devices aren’t at risk of being captured by a botnet. Krebs points out that default passwords are the most likely culprit. If you have never changed the password that came with your device, now’s the time. Before you do, you’ll need to reset the product back to its factory settings. This ought to wipe any malicious code that has found a home — changing the password without doing a factory reset simply tells the owners of the botnet your new password.
Krebs also advises that at this point, you should make sure the device is running the latest firmware, something he acknowledges can be really tricky on some of the more user-unfriendly products on the market.
Some devices have a default password that’s unknown to the user, and which can’t be changed.
With all of that said, it’s possible there’s nothing you can do — except not use the device. The potency of the Mirai botnet is due to the fact some poorly designed devices have a default password that’s unknown to the user, and not controlled by the user interface. Backdoors like this are sometimes left behind by companies to make troubleshooting a device easier, to make the device more appealing to partner businesses that might want to use it, and to have an easy way to access all devices quickly. But it’s a huge security flaw, and often, not one you can fix.
We don’t know all the devices that have this problem, but Brian Krebs did do some digging that allowed him to identify a handful.
Taking a device offline can be painful. You paid for it, after all. But the besides providing an opportunity for botnets, insecure devices can lead to personal security concerns. The backdoor used by the botnet could also, in many cases, be used to change device settings without your knowledge.
What about next time?
If your favorite website becomes the victim of a DDoS attack, there’s probably not much you can do but wait it out. But if a DNS provider like Dyn should be attacked, your best bet is to switch your DNS provider from your local ISP to a service like Google DNS or Open DNS.
“That’s a great approach,” Andrew Campbell, founder of Brickhost.com, a Canadian web hosting company, told us. “There are other benefits too. Sites will not only load faster, they’ll be more reliable.”
That’s because your local ISP’s DNS infrastructure isn’t as robust as these bigger companies, and may cache DNS information for longer periods of time. When Dyn was attacked, Campbell says it would have immediately changed the pathways to its clients’ sites, but it can take smaller DNS services up to 24 hours to reflect such a change. In the meantime, you’ll still be sent to an address that’s under siege from the attack and the site won’t respond.
Another benefit to using a third-party DNS provider is security. Occasionally DNS records can be hacked and legitimate domains can end up sending users to phishing sites or worse. There’s some evidence that these threats are better mitigated when you use DNS from Google or Open DNS.
Editors' Recommendations
- Europe just suffered its worst DDoS attack ever, but we don’t know why
- How to stop your emails from being tracked, and preserve your privacy
- How to keep your data secure while working from home



