(in)Secure is a weekly column that dives into the rapidly escalating topic of cybersecurity.
Another day, another malware attack. Regardless of how much money is poured into increasing cybersecurity, the situation doesn’t seem to improve. Could machine learning that adapts to new methods be the solution?
For some companies, such machine learning techniques go hand in hand with more traditional signature based detection and others employ behavioral learning to watch out for other, unspecified threats. For threat prevention company Cylance, however, machine learning is all it needs to offer what it claims is the most effective anti-malware solution available today.
Like Google’s Sundar Pinchai championed last year, Cylance is putting AI-first in its new consumer-facing antimalware solution. But more than that, it’s putting AI-only in its flagship security software, which it claims is more than enough to stifle the malware threats of yesterday, today, and tomorrow.
All you need is love… of AI
“If you look at it historically, all of the technology from legacy vendors really goes back to the 1990s which operates under the premise that somebody needs to get infected for the rest to be protected,” Cylance senior VP, Christopher Bray, told Digital Trends. “That worked very well and in the 90s and early 2000s, when you just had a handful of viruses being released every month, you could get an update to end users [quickly].”

Today though, he explained, things are quite different. Citing that there are more than 350,000 new pieces of malware released every single day, such signature-based anti-malware solutions just don’t cut it, he said.
The types of threats facing consumers, businesses, and the security companies who protect them all are different too. While spam and adware are still prevalent, new threats like ransomware and cryptojacking have become commonplace. With these new and ever growing attacks, Cylance believes that machine learning and AI-driven smart software is the only real way to combat it.
“[Machine learning] does not cover ALL types of malware and threats, and is much more prone to false positives”
“We’ve trained an algorithm. We’ve trained it with samples of good and samples of bad software,” he said. “The smart antivirus product which resides on a desktop Mac or a PC and inspects every file that tries to execute and before it can run you’ll analyze it and say, hey, is this good or is this bad and if it’s bad. It’ll quarantine it.”
This, Bray claims, is all you really need. But is that really true?
AI competition
Relying solely on machine learning is not an approach other anti-malware companies are taking, even ones that incorporate AI into the process. While Bray might have a glowing opinion of Cylance’s own machine learning, other companies do use it too. Kaspersky, Malwarebytes, McAfee, and many others, all utilize machine learning to help detect malicious software, they just tend to do it alongside more traditional techniques.
So what’s so different about Cylance’s solution?
“What we’re seeing from the industry right now in the consumer space, machine learning seems to be applied to triaging [the] identifying [of] malicious software and writing fixes for it,” Bray said. “So, it’s still the old model. It’s just faster. With the volume of most software out there. It doesn’t matter how fast you are if you get a signature up 15 minutes or five minutes as these threats propagate within seconds globally. We don’t view [their machine learning] as an AI solution like ours.”
It would be unfair to categorize such a statement as anything other than opinion – one that we’re sure other antivirus companies would contest.
“It uses the power of it’s learning of his training to look at that and say, ‘Okay, this is good. I’ll let it run or no, this is bad.’”
Indeed we’ve seen anti-ransomware protections from the likes of Malwarebytes and Zone Alarm offer similar analaytical software that looks at processes as they begin to run and if they detect malicious behavior in their application, halts them in their tracks and in some cases rolls back any changes that they made.
Furthermore, according to Malwarebytes, there are some serious problems with relying solely on machine learning for threat detection.
“It does not cover ALL types of malware and threats, and is much more prone to false positives,” Pedro Bustamante, the VP of Products & Research at Malwarebytes, told us. “[We] implement machine learning as one of the detection layers in its protection stack. It is not the main layer, but it is an important layer.”
Clearly, Bustamante doesn’t think machine learning is the end-all, be-all from a malware detection point of view. He even stated that he couldn’t foresee a time when machine learning would be all that was needed for anti-malware software.
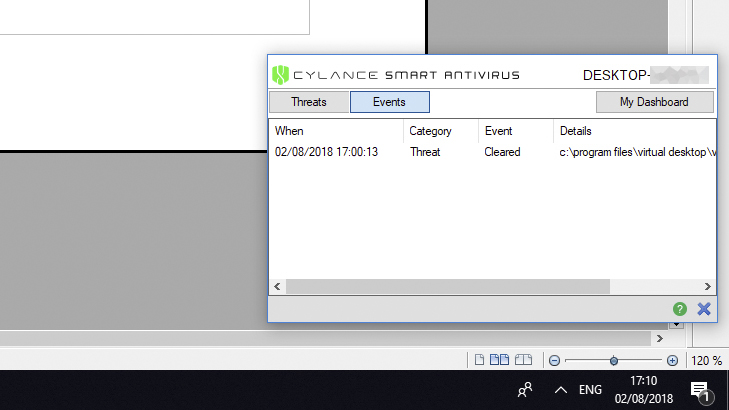
Cylance doesn’t have a dedicated scan function; it focuses entirely on live protection.
Still, Bray was adamant that Cylance’s solution is quite different. Nailing him down on the specifics of what makes it so wasn’t easy, but he explained the AI further by stating that it’s been trained on millions of attributes that could suggest “good and bad behavior,” as he put it.
“[The algorithm] essentially analyzes any piece of software that runs on that device and before that software can run it uses the power of it’s learning of his training to look at that and say, ‘Okay, this is good. I’ll let it run or no, this is bad,'” he said.
Analysis over scans
One area where Cylance’s antiviral solution is distinctly different than most, is that it doesn’t offer any sort of remediation scanning function with its software. Scans have been at the heart of most antivirus software for decades, but to Cylance, that’s more akin to closing the door after the horse has bolted.
Instead, it focuses entirely on live protection, making sure threats are detected before they even start having an impact on a system. The upside of this, Bray tells us, is that its software has a very small footprint on the system it’s installed on and requires far less resources to run.

“Because [Cylance AV] doesn’t need to churn through your hard drive and run all of these scans, the resource impact is is significantly lower than a legacy solution,” he said. “If you think about a legacy solution, it’s […] got this database of signature files that it then needs to reference every time it’s checking something — just by virtue of going back and forth and checking the signature file list.”
By avoiding that, Bray claims, Cylance Smart Antvirius is far less taxing on a system. In some very rudimentary testing of this claim, we found it to be a bit of a mixed bag.
“With our solution, our philosophy is ‘hey, you know what, go click on whatever you feel like, we’ve got your back.'”
When no new applications were opened, we found the client to be very lightweight, consuming no more than a few megabytes of RAM and almost zero percent of our (Intel Core i5-4690k) CPU. However, upon opening new applications, we did see significant spikes in CPU usage, in one case (when opening Adobe Acrobat DC) it required as much as 50 percent of the test system’s CPU for a few seconds.
In comparison, Malwarebytes Antimalware, which was also running on that same system, required close to 150MB of RAM while idling, but typically only required a few percent of the CPU’s cycles when opening new applications.
However, Malwarebytes did continue to show such numbers upon repeat opening of the same applications, while Cylance’s solution appeared to learn that such apps were not malicious and required far less resources on repeat launches.

These tests are far from conclusive, but do appear to highlight the difference between anti-malware solutions when it comes to resources required for tracking potentially dangerous processes running on a system.
Predictive policing under the hood
Regardless of everything else Cylance’s Smart Antivirus does, the one feature Bray was most proud of was its ability to detect “unknown” threats. That is, malware that has yet to be written or even effectively categorized. By relying heavily on analysis of process behavior, he claims that Cylance’s security software is capable of handling threats that no one has ever seen before.
“With an AI based solution, an application that can identify the characteristic of malicious software, it doesn’t matter if it’s known or unknown,” he said. “You can say, hey, this thing is bad and make split-second decisions.”
New types of ransomware attacks is one area where he feels that the software is particularly good at combating. Citing the WannaCry ransomware attack from mid-2017, Bray claimed that Cylance fed the malicious software to a copy of its algorithm from two years prior, and that it was able to detect the ransomware and stop it in its tracks, despite predating its creation by some time.
That same applies to new ransomware attacks, he said, which are stopped before they even start and the end user is none the wiser.
Operating seamlessly out of the line of sight of consumers was something that he and Cylance truly believe in, removing the emphasis of knowledge and oversight from the consumer.
“Over the years, people have gotten accustomed to [thinking] ‘Okay, I am running security software but I shouldn’t have double clicked on that and that’s why I’m infected,'” he said. “With our solution, our philosophy is ‘hey, you know what, go click on whatever you feel like, we’ve got your back.'”
Even if Cylance’s AI-driven Smart Antivirus isn’t quite perhaps as revolutionary as its marketing might suggest, it is certainly a leaner and more focused approach to cybersecurity. If it can predict and stop the next WannaCry, we’ll happily let AI take the wheel.
Editors' Recommendations
- A.I. doesn’t usually forget anything, but Facebook’s new system does. Here’s why
- How A.I. created that amazing sports highlight reel you can’t stop watching