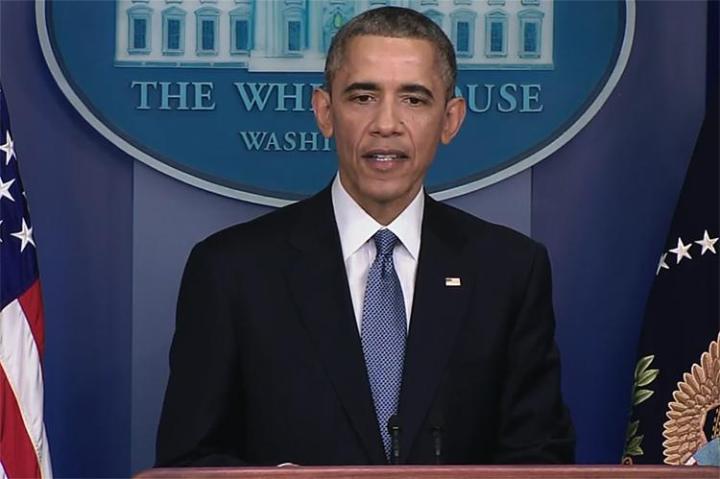
Update 12/19/2014 11:17am Pacific: In a press conference President Obama took a question asking if he thought Sony did the right thing by pulling The Interview. He responded “I am sympathetic to the concerns they faced. Having said that, yes, I think they made a mistake.” He went on to say that the United States can’t tolerate a situation where “publishers start engaging in self-censorship because they don’t want to offend the sensibilities of someone whose sensibilities probably need to be offended.”
The President also said further action will be taken by the government. “[They] caused a lot of damage, and we will respond. We will respond proportionally, in a time and manner we choose.” He did not clarify what the response might be. Further, he said there’s currently no reason to believe North Korea acted in conjunction with any other country or organization.
A new statement posted on the FBI’s official website makes it clear: North Korea is the party responsible for the attack on Sony Pictures. This is the first announcement from a U.S. intelligence or law enforcement agency made on the record, and it all but confirms that widespread speculation about the nation’s culpability was correct.
The FBI has been working with Sony since the first few hours of the attack in an attempt to minimize the damage and figure out who was responsible. In the weeks that have passed, several key pieces of evidence have been discovered which point the finger directly at North Korea.
Perhaps the most damning point is the use of techniques and malware that the FBI has linked to North Korea in the past. Software used for sophisticated attacks such as those deployed by The Guardians of Peace require custom solutions, and hacking organizations often re-deploy malware when possible rather than waste time re-writing it from scratch. Consider it a digital fingerprint.
A link has also formed between the infrastructure used for this attack and that used for past attacks on U.S. institutions by North Korea. I.P. addresses known to belong to the nation-states computers were connected to the Sony hack. The addresses were coded into the malware itself, presumably so it could communicate with its masters.
The statement goes on to say that “North Korea’s attack on Sony Pictures Entertainment (SPE) reaffirms that cyber threats pose one of the gravest national security dangers to the United States.” It goes on to re-affirm the FBI’s commitment to supporting any company that finds itself victim of a cyber attack, no matter the source.
Everyone already suspected the country’s involvement, so the FBI’s words are no surprise, but the fact that a U.S. government agency has pointed the finger is significant and suggests some form of diplomatic response may be in the works. President Obama is due to give an end-of-year press conference today, December 19th, before he leaves for his Christmas vacation. It would be an ideal time for the President to outline the government’s response if one is indeed intended.


