- Home
- Computing
Computing
About
News, reviews, and discussion about desktop PCs, laptops, and everything else in the world of computing, including in-depth buying guides and daily videos.

Own an RTX 4090? We have some bad news





This new VR headset beats the Vision Pro in one key way and is half the price

The world’s first 8K mini-LED monitor has arrived

One of Lenovo’s best-selling ThinkPad laptops is 45% off today

Best tools to stress test your CPU


Apple already has its next big chip, but you may never see it

You can still buy the M1 MacBook Air, and it’s cheaper than ever

Save $650 on this Lenovo gaming PC with an RTX 4080 Super

This Lenovo gaming laptop with an RTX 4090 is $740 off today

The 7 best laptop stands in 2024

The 5 best MacBooks for video editing in 2024

How to create folders in Gmail
Meta Quest 4: Here’s what we want from the next big VR headset

Is ExpressVPN free? A breakdown of the popular VPN’s costs

How to select multiple files on a Mac

Ray tracing vs. path tracing — which is the best dynamic lighting technique?

Does ExpressVPN work on a Chromebook?

Paint for Mac doesn’t exist, but here are some alternatives

How to take a screenshot on a Mac

How to keep your laptop battery healthy and extend its life

How to connect an iPhone to a Mac with or without a cable

HP Envy vs. Pavilion: Which is the better laptop line?
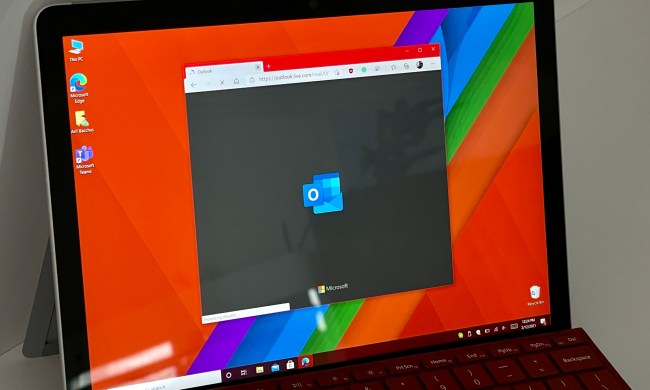
How to share your Outlook calendar
Computing News
Laptops
Computing Reviews
Computing Guides
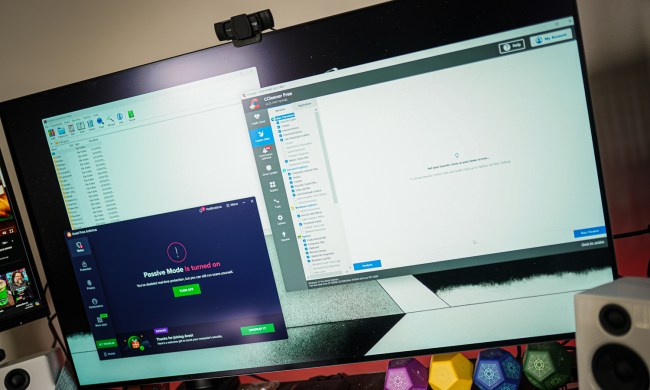
Luke Larsen is a Senior Editor at Digital Trends and manages all content covering laptops, monitors, PC hardware, and everything else that plugs into a computer. Luke joined Digital Trends in 2017 as a native Portlander, happy to join a media company that called his city home. His obsession with technology is in observing the ebb and flow of how technological advancement and product design intersects with our day-to-day experience of it. From digging into the minute details to stepping back and seeing the wider trends, Luke revels in telling stories with tech.
Before working at DT, he worked as Tech Editor at Paste Magazine for over four years and has bylines at publications such as IGN and The Oregonian. When he’s not obsessing over what the best laptop is or how Apple can fix the Mac, Luke spends his time playing designer board games, quoting obscure Star Wars lines, and hanging with his family.