A new zero-day vulnerability in Microsoft Office could potentially allow hackers to take control of your computer. The vulnerability can be exploited even if you don’t actually open an infected file.
Although we’re still waiting for an official fix, Microsoft has released a workaround for this exploit, so if you frequently use MS Office, be sure to check it out.
Interesting maldoc was submitted from Belarus. It uses Word's external link to load the HTML and then uses the "ms-msdt" scheme to execute PowerShell code.https://t.co/hTdAfHOUx3 pic.twitter.com/rVSb02ZTwt
— nao_sec (@nao_sec) May 27, 2022
The vulnerability has been dubbed Follina by one of the researchers who first looked into it — Kevin Beaumont, who also wrote a lengthy post about it. It first came to light on May 27 through a tweet by nao_sec, although Microsoft allegedly first heard of it as early as April. Although no patch has been released for it just yet, Microsoft’s workaround involves disabling the Microsoft Support Diagnostic Tool (MSDT), which is how the exploit gets entry into the attacked computer.
This exploit affects primarily .rtf files, but other MS Word files can also be affected. A feature in MS Word called Templates allows the program to load and execute code from external sources. Follina relies on this in order to enter the computer and then runs a series of commands that opens up MSDT. Under regular circumstances, MSDT is a safe tool that Microsoft uses to debug various issues for Windows users. Unfortunately, in this case, it also grants remote access to your computer, which helps the exploit take control of it.
In the case of .rtf files, the exploit can run even if you don’t open the file. As long as you view it in File Explorer, Follina can be executed. Once the attacker gains control of your computer via MSDT, it’s up to them as far as what they want to do. They might download malicious software, leak files, and do pretty much everything else.
Beaumont has shared plenty of examples of the way Follina has already been exploited and found in various files. The exploit is being used for financial extortion, among other things. Needless to say — you don’t want this on your computer.
What do you do until Microsoft releases a patch?
There are a few steps you can take to stay safe from the Follina exploit until Microsoft itself releases a patch that will fix this problem. As things stand now, the workaround is the official fix, and we don’t know for a fact that anything else is sure to follow.
First and foremost, check whether your version of Microsoft Office could potentially be affected. So far, the vulnerability has been found in Office 2013, 2016, 2019, 2021, Office ProPlus, and Office 365. There is no telling whether older versions of Microsoft Office are safe, though, so it’s better to take additional steps to protect yourself.
If you’re able to avoid using .doc, .docx, and .rtf files for the time being, it’s not a bad idea. Consider switching to cloud-based alternatives like Google Docs. Only accept and download files from 100%-proven sources — which is a good guideline to live by, in general.
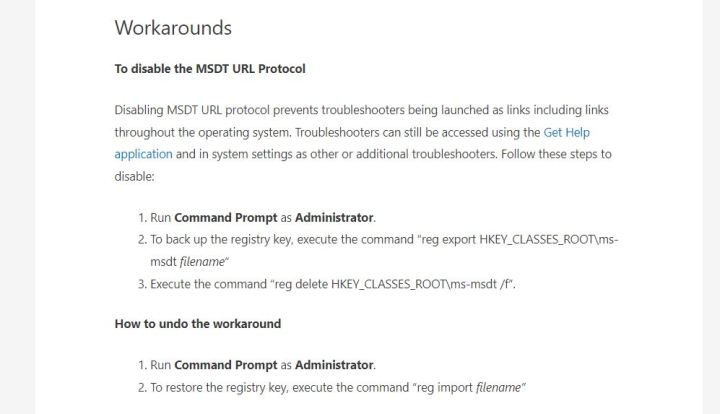
Last but not least, follow Microsoft’s guidance on disabling MSDT. It will require you to open the Command Prompt and run it as administrator, then input a couple of entries. If everything goes through as planned, you should be safe from Follina. Nevertheless, remember to always be cautious.
Editors' Recommendations
- How Intel and Microsoft are teaming up to take on Apple
- 7 beloved Windows apps that Microsoft has killed over the years
- You can finally purge your PC of default Windows apps
- Microsoft accidentally released 38TB of private data in a major leak
- Hackers are sending malware through seemingly innocent Microsoft Teams messages




