Android’s security woes need no introduction, but another threat that hasn’t received its fair share of awareness relates to spyware and stalkerware apps. These apps can secretly be installed on a victim’s phone to monitor their activity and can be exploited to harass victims of domestic abuse and engage in online stalking. All someone needs is physical access to the victim’s phone to install these apps, which is not too difficult in cases of domestic abuse.
Call it an app-fueled version of AirTag stalking, but on steroids, because these spyware apps can steal everything including messages, call logs, emails, photos, and videos. Some can even activate the microphone and the camera, and secretly transfer these recordings to a remote server where the abuser can access it. Since Google Play’s policies don’t allow stalking apps, these apps are sold via third-party websites and need to be sideloaded.

As dangerous as it all sounds, the situation is even more grim due to the lack of of defense mechanisms on Android phones, especially for folks that aren’t particularly tech-savvy. A collaborative research effort led by Alex Liu from the University of California, San Diego, studied 14 stalkerware apps that are readily available from third-party online websites — and found them loaded with some extremely worrying capabilities.
An unprecedented scope of damage
In terms of their basic capabilities, these apps were able to access calendar entries, call logs, clipboard entries, contacts, information pulled from other applications installed on the victim’s phone, location details, network information, phone details, messages, and media files.
A majority of these apps were also able to secretly access the camera feed and the microphone for multimedia capture, taking screenshots via a remote command and even accessing protected data. But that’s not where the horror tale ends.
Eleven of the studied apps tried to obscure the process of uninstalling them, while every single one of the spyware apps came coded with a “die-hard” functionality that allowed it to automatically start after a reboot or after memory clearance by the Android system. Such apps are known to disable the “Force Stop” and “Uninstall” buttons in some cases.
One would think that a quick look at the app launcher would alert the victim about any suspicious apps installed on their phones. But that privilege is not really available to victims of these spyware apps, which can cost anywhere between $30 to $100 with a subscription model.
Hiding, manipulating, and playing the system
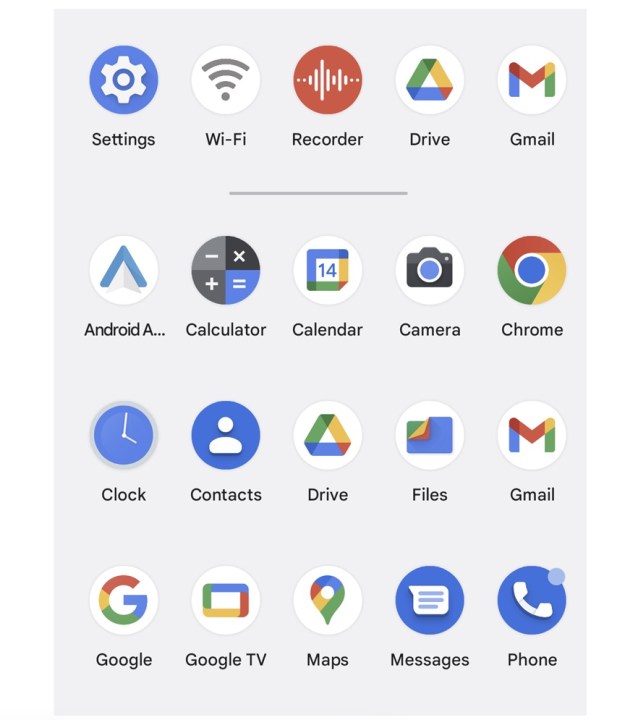
Liu, lead author of the research paper, told Digital Trends in an interview that most of these apps try to hide or use “innocent” names and iconography to avoid suspicion. For example, 11 out of the 14 spyware apps tried to hide in plain sight under the guise of apps with names like “Wi-Fi,” “Internet Service,” and “SyncServices,” complete with believable system icons to help avoid any suspicion.
Since these are core services for a phone, a lot of users won’t want to engage with them out of fear that it would break the corresponding systems on their phone. But there’s more to the threat factor here. “We’ve also seen advanced cases where these apps are able to hide on the app screen or the app launcher,” Liu said.
Some of these apps actively tried to hide the application icon after being installed so that the victim would never guess that surveillance software was active on their phone. Moreover, most of these apps, despite running in the background and abusing Android’s permissions system, don’t appear on the recent apps screen.
“If you don’t see it, how do you know.”
Digital Trends asked Liu if these spyware apps that are secretly running in the background, collecting sensitive personal information, can pop up in the so-called cleaner apps that advise users to uninstall apps they haven’t used in a while. Liu, who is going to present the findings at a conference in Zurich this summer, says the team didn’t explore that possibility.
However, chances are slim that these storage cleaner apps would flag the spyware apps as redundant because these apps are always running in the background and won’t be flagged as inactive. But the sheer ingenuity that some of these apps employ is the stuff of privacy nightmares.
Sneaky, risky, and extremely leak-prone
When you launch the camera in any app, you see a preview of what’s in front of the camera. Some of these apps shrink the preview size to 1×1 pixel or even make the preview transparent, which makes it impossible to detect if a stalking app is recording a video or sending the live view to a remote server.
Some of these don’t even show a preview, directly capturing the video and transmitting it secretly. One of these apps, called Spy24, uses a secret browser system to stream full-resolution camera footage. Phone call and voice recording is also a fairly common trait among these applications.
The studied stalkerware apps were also found to abuse the accessibility settings on Android. For example, users with visual or hearing impairment have the phone read out the on-screen contents. This loophole allows these apps to read content from other apps running on the screen, extract data from notifications, and even avoid the read receipt trigger.
The spyware apps further abuse the accessibility system for keystroke logging, which is a common way to steal sensitive information such as log-in credentials for wallets and banking systems. Some of the apps that were studied relied on an SMS system, which involves the bad actor sending an SMS to activate certain functionalities.
But in a few cases, not even an activation SMS was needed to do the job. One of the apps (called Spapp) is capable of remotely wiping all the data on the victim’s phone using just an SMS. A hacker can send random messages with different passcode combinations to do it, even without the abuser knowing it, which further compounds the risk factor.

While these readily available spyware apps are dangerous on their own, another aspect that raises concern is their weak security when it comes to storing stolen personal information. A healthy bunch of these apps transmitted the data over unencrypted HTTP connections, which means a bad actor can eavesdrop on the Wi-Fi network and gain access to all of it.
Six of the apps stored all the stolen media in public URLs, assigning random numbers to the data packets. A hacker could play with these random digits to steal data associated with not just one, but multiple accounts deployed across different devices for spying on random victims. In some cases, the spyware apps’ servers continue to harvest data even after the subscription license is expired.
What can you do?
So, how can a regular smartphone user avoid becoming the next victim of these spyware apps? Liu says that would require proactive action because Android doesn’t have any automated system to alert you about spyware apps. “There is no definitive way of knowing if there’s something wrong with your phone,” Liu stresses.
However, you can look for certain signs. “These apps are continuously running in the background, so you would come across abnormally high battery usage,” Liu tells me. “That’s how you know something might be wrong.” Liu also highlights Android’s sensor alert system, which now shows an icon at the top when the camera or mic is being used by an app.
Liu, who is a Ph.D. student at the university’s computer science department, says that if your mobile data usage has suddenly gone up, that’s also a sign that something is wrong because these spyware apps are constantly sending large packets of data, including media files, emails logs, etc. to a remote server.

Another foolproof way of finding these shady apps, especially those that hide from the app launcher, is to check the list of all apps installed on your phone from within the Settings app. If you see any apps that look suspicious, it makes sense to get rid of them. “You should go through every app and see if you recognize them or not. That’s the ultimate solution because no app can hide there,” Liu adds.
Finally, you also have the Privacy Dashboard, a feature introduced with Android 12, that lets you see all the permissions granted to each app. For privacy-conscious users, it is advisable to revoke the permissions that they think a certain app shouldn’t have in the first place. The Quick Settings panel, which can be accessed by swiping down from the top edge, lets users disable mic and camera access if any app is using those permissions in the background.
“But at the end of the day, you require some technical expertise,” Liu concludes. That’s not how the situation should ideally be for hundreds of millions of Android smartphone users. Liu, and the rest of the team behind the research paper, have a list of guidelines and suggestions for Google to ensure that
Editors' Recommendations
- Google Messages vs. Samsung Messages: Which app should you use?
- The 1Password Android app just got a huge upgrade
- Google is launching a powerful new AI app for your Android phone
- These are my 8 favorite charity apps for iPhone and Android
- ChatGPT app arrives for Android, but there’s a catch




