One possible threat is explored in a new study by researchers at the University at Buffalo in New York entitled “My Smartphone Knows What You Print: Exploring Smartphone-Based Side-Channel Attacks Against 3D Printers.”
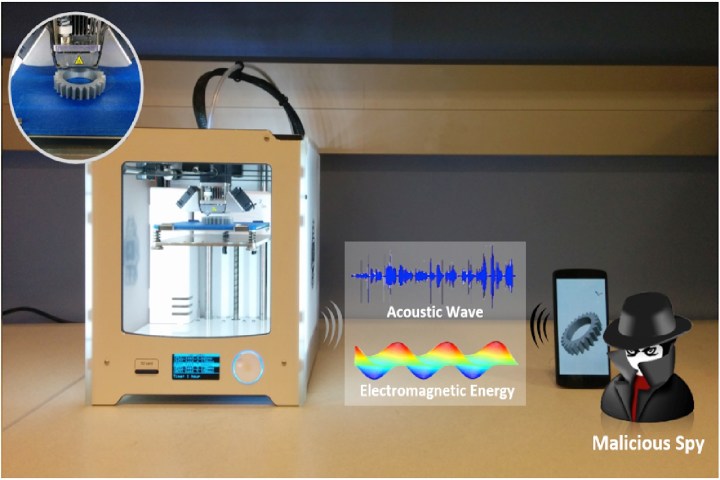
A team of computer scientists was able to use a regular smartphone’s built-in sensors to measure the electromagnetic energy and acoustic waves that emanate from a 3-D printer. By doing so, they were then able to gather enough data to replicate 3D-printed objects with accuracy levels of up to 94 percent, depending on the complexity of the object.
“This is the first work to investigate the vulnerability of 3D printers,” Wenyao Xu, assistant professor in the unicersity’s department of computer science and engineering, told Digital Trends. “Considering that 3D printers are the driving force for innovation and an emerging manufacturing approach, it is very critical to make sure 3D printers are secure, and the intellectual property in the 3D design is well-protected.”
Xu said that very few people are aware of the potential danger to 3D printers posed by nothing more sinister than the ubiquitous smartphone.
“This attack can happen in both individual and industrial 3D printers,” Xu continued. “Also, it can be applied against bioprinting and metal printing, which are more security sensitive.”
Fortunately, noone can accuse Xu and his fellow researchers of being the kind of folks to point out a problem, then offer no solution.
One possible answer involves hardware-based concepts like acoustic and electromagnetic shields. Another may turn out to be even simpler. “We have proposed new path planning algorithms to spoof the side-channel attack,” Xu said. “No extra hardware is needed to prevent this threat.”


