- Home
- Computing
Computing
About
News, reviews, and discussion about desktop PCs, laptops, and everything else in the world of computing, including in-depth buying guides and daily videos.

Meta has a bold new strategy for VR






The most common Skype problems and how to fix them

The 6 best laptops for realtors in 2024

How to convert WMA to MP3 on Mac, Windows, and Web

How to convert FLAC to MP3 on Mac, Windows, and web


How to convert M4A files to MP3 on Mac, Windows, and web
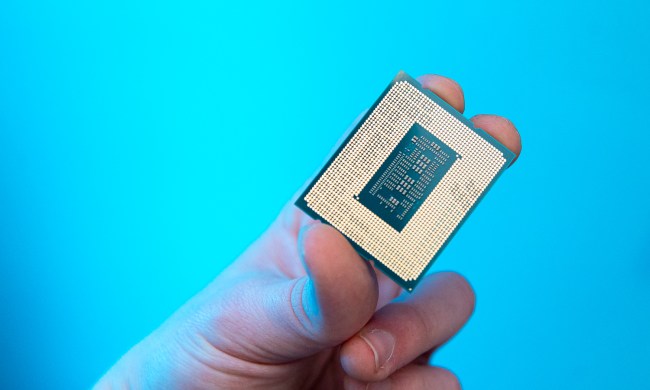
How hot is too hot for your CPU?

The most common Windows 11 problems and how to fix them

The 6 best tablets for college in 2024

How I unlocked the hidden modes of DLSS
How to cancel a Twitch subscription on desktop or mobile

How to tell if your webcam has been hacked

The most common Microsoft Teams problems and how to fix them
NordVPN free trial: Try the service for free for a month

How to convert a PDF to JPG on Mac, Windows, and web

The 6 best laptops for engineers in 2024

How to download YouTube videos for offline viewing

How to cancel Spotify Premium on any device

How to delete your ChatGPT account

How to cancel your ChatGPT Plus subscription

How to factory reset Windows 10 or Windows 11

How to find a Wi-Fi password on Mac

How to get GPT-4 for free
Computing News
Laptops
Computing Reviews
Nvidia
Luke Larsen is a Senior Editor at Digital Trends and manages all content covering laptops, monitors, PC hardware, and everything else that plugs into a computer. Luke joined Digital Trends in 2017 as a native Portlander, happy to join a media company that called his city home. His obsession with technology is in observing the ebb and flow of how technological advancement and product design intersects with our day-to-day experience of it. From digging into the minute details to stepping back and seeing the wider trends, Luke revels in telling stories with tech.
Before working at DT, he worked as Tech Editor at Paste Magazine for over four years and has bylines at publications such as IGN and The Oregonian. When he’s not obsessing over what the best laptop is or how Apple can fix the Mac, Luke spends his time playing designer board games, quoting obscure Star Wars lines, and hanging with his family.