- Home
- Computing
Computing
About
News, reviews, and discussion about desktop PCs, laptops, and everything else in the world of computing, including in-depth buying guides and daily videos.

The best 17-inch laptop deals from HP, LG, Razer, and more








These are the 10 best gaming PCs I’d recommend to anyone

Get this Asus laptop with a year of Microsoft Office for $199

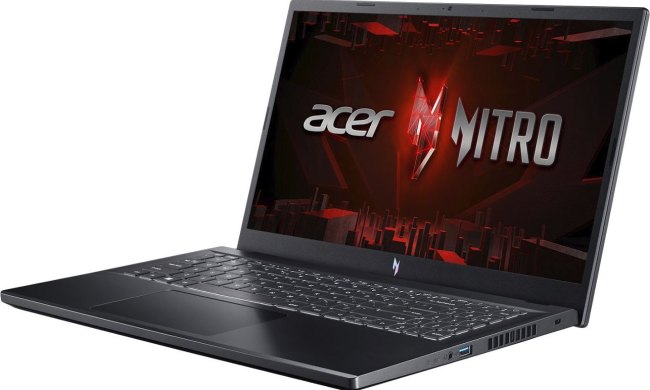
Save $400 on this Razer gaming laptop with an RTX 4060

Snag a year’s access to Norton’s ‘Secure VPN’ while it’s 75% off


How to change margins in Google Docs

How to alphabetize lists in Microsoft Word

How to build a table of contents in Microsoft Word
How to alphabetize data in an Excel spreadsheet
How to delete your Gmail account (and what you need to know)

Windows 11 might nag you about AI requirements soon

How to delete a file from Google Drive on desktop and mobile

The best tablets in 2024: top 11 tablets you can buy now

Hyte made me fall in love with my gaming PC all over again
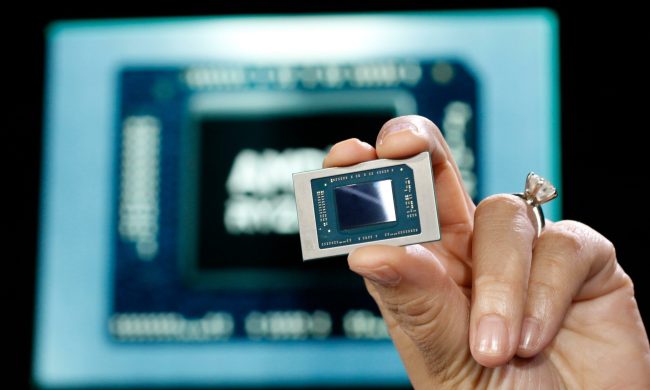
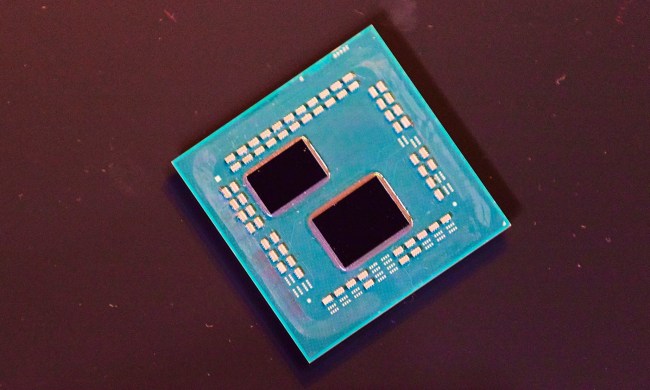
AMD’s upcoming APUs might destroy your GPU

How to draw on Google Docs to add doodles, sketches, and more

Best gaming chair deals: Save on Corsair, Razer, and more

How to delete files on a Chromebook

Amazon deals: TVs, laptops, headphones and more

The best laptop brands for 2024

How to delete messages on your Mac
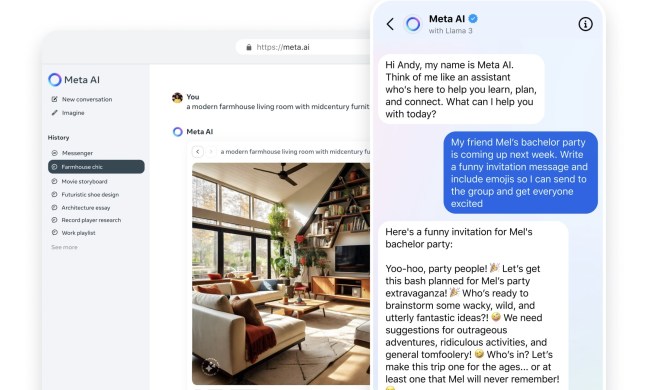
Why Llama 3 is changing everything in the world of AI

How to delete or hide chats in Microsoft Teams
Computing News
Laptops
Computing Reviews
Nvidia
Luke Larsen is a Senior Editor at Digital Trends and manages all content covering laptops, monitors, PC hardware, and everything else that plugs into a computer. Luke joined Digital Trends in 2017 as a native Portlander, happy to join a media company that called his city home. His obsession with technology is in observing the ebb and flow of how technological advancement and product design intersects with our day-to-day experience of it. From digging into the minute details to stepping back and seeing the wider trends, Luke revels in telling stories with tech.
Before working at DT, he worked as Tech Editor at Paste Magazine for over four years and has bylines at publications such as IGN and The Oregonian. When he’s not obsessing over what the best laptop is or how Apple can fix the Mac, Luke spends his time playing designer board games, quoting obscure Star Wars lines, and hanging with his family.